When the Water Stops and the Money Vanishes: Cyber Threats to National Lifelines
Two major incidents in Europe—the hacking of a Norwegian dam and a phishing breach at the UK’s tax office—underscore the escalating vulnerability of critical infrastructure to digital attacks.
At first glance, there may seem little connection between a remote hydroelectric dam in Norway and the sprawling digital bureaucracy of the UK’s tax system. Yet both were the targets of highly impactful cyber attacks—breaches that not only disrupted services but exposed weaknesses in the digital backbone of modern society.
The two incidents offer a sobering glimpse into the evolving tactics of cybercriminals—and a warning for every country relying on legacy systems to support essential services.
1. Norwegian Dam Hack: Critical Infrastructure on the Brink
A System Breach with Water Supply Implications
In early June 2025, Norwegian authorities confirmed a cyberattack had breached the operational systems of a regional water utility responsible for dam control at the Lake Risevatnet dam near the city of Svelgen in Southwest Norway. According to the Norwegian National Security Authority (NSM), attackers were able to manipulate industrial control systems (ICS), affecting water flow through the infrastructure. Fortunately, no catastrophic flooding or structural damage occurred, but the disruption highlighted the potential danger.
The incident was widely reported in Norwegian media and by national security authorities. The breach originated through the utility’s IT environment and moved laterally into its operational technology (OT) systems—systems that control physical equipment such as pumps, turbines and valves.
This breakdown of isolation between IT and OT is a known risk across many critical infrastructure sectors. As more industrial systems adopt remote management and connect to cloud-based platforms, they become increasingly exposed to the kinds of attacks once confined to traditional IT networks.
The key concern here is not the immediate damage—though that alone is serious—but the precedent. Attackers successfully reached into the physical layer of a critical utility. If that boundary can be crossed in one location, it can be crossed elsewhere.
OT Security: An Overdue Priority
The recent cyber breach underscores a systemic and long-standing vulnerability across many public utilities and building management systems: the absence of effective segmentation between operational technology (OT) and IT networks.
This weakness isn’t new—but it’s becoming more dangerous as legacy infrastructure is increasingly connected to corporate IT systems without adequate controls.
In Dragos’s 2025 OT Cybersecurity Year in Review, the company reports that over 70% of assessed industrial environments in Europe lacked effective segmentation or logging between IT and OT systems—a critical vulnerability in the face of rising cyber threats to infrastructure
Dragos’ report revealed that 86% of OT-targeted attacks in 2023 involved lateral movement from IT environments—a scenario echoed in the Norwegian breach.
As more building management networks—including HVAC, access control, and energy systems—merge with corporate IT environments, the risks associated with poor segmentation will only intensify. Without real-time monitoring, access controls, and strict network boundaries, these environments remain prime targets for lateral movement and disruption.
2. UK Tax Authority Phishing Attack: £47 Million Lost
Social Engineering at Scale
The UK’s HM Revenue and Customs (HMRC) confirmed on 19 June 2025 that a phishing campaign had compromised around 100,000 taxpayer accounts, resulting in direct losses totalling £47 million.
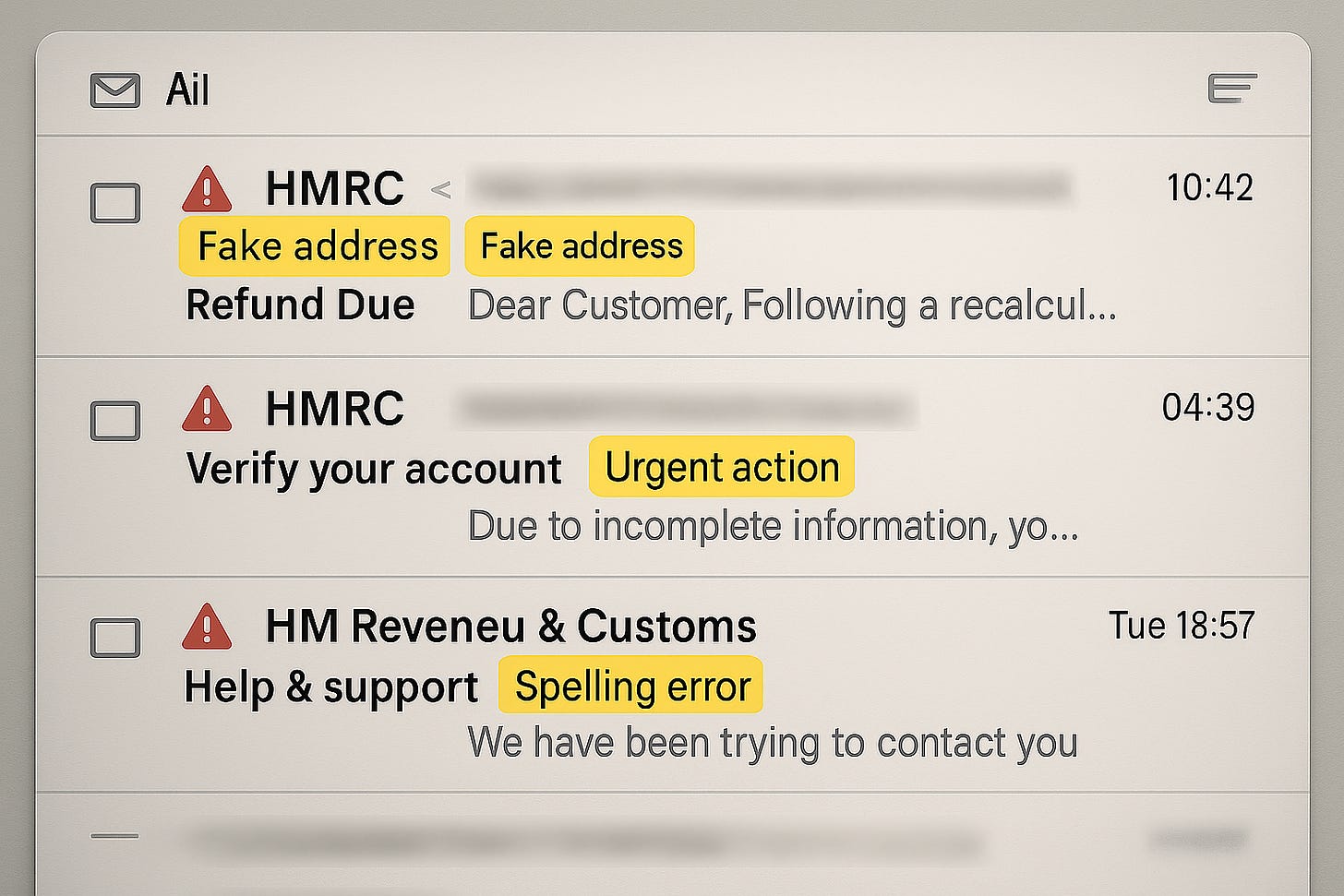
The phishing campaign relied on impersonating HMRC through emails and texts that led victims to spoofed login pages. This form of social engineering—targeting people rather than systems—is increasingly effective. Many users were tricked into revealing their credentials, which were then used to bypass authentication and file claims.
While HMRC and the National Cyber Security Centre (NCSC) have issued statements and guidance in response, the damage demonstrates that even the most security-aware departments are not immune.
More importantly, the breach raises serious questions about the resilience of public digital services. As citizens are required to do more online—from paying taxes to accessing healthcare—identity verification systems must evolve to withstand modern attacks
The Rise—and Cost—of Phishing in the UK
Phishing remains the number one attack vector in the UK. According to the UK Govt Cyber Security Breaches Survey 2025, over 84% of medium to large UK businesses identified phishing as their most frequent cyber threat.
Phishing remains the leading cybercrime vector—93% of businesses and 95% of charities affected by cybercrime via phishing.
More alarming is the trend towards multi-channel phishing, where attackers use combinations of email, SMS, and even voice calls to impersonate trusted entities.
Expert Reactions: Warnings and Solutions
On Infrastructure Cybersecurity:
“Europe must prioritise ICS and SCADA security with the same urgency it affords energy transition,” said Ciaran Martin, former head of the UK’s NCSC, in a commentary to digital journal Just Security. “OT systems are no longer isolated. Every digital interface is a potential entry point.”
The European Union Agency for Cybersecurity (ENISA) has consistently warned about the cybersecurity risks linked to IT/OT convergence, particularly in critical sectors such as space, energy, and manufacturing. Its 2025 Space Threat Landscape report cites weak network segmentation and legacy vulnerabilities as major enablers for cyberattacks on satellite and ground systems, especially where operational and IT domains intersect.
On Human Factors in Phishing:
The Information Commissioner’s Office (ICO) has already launched an inquiry into HMRC’s handling of taxpayer data, while urging other departments to adopt stronger citizen-facing MFA processes.
Renowned social-engineer Jenny Radcliffe has emphasised that human error—not software—is often the weakest link. As she told the Easy Prey podcast:
“With social engineering, we only need one person to make the mistake to let me through a door and it’s breached.”
She also described human‑targeted attacks as being “every bit as lethal as a technical hack, but not using technical means.” These insights underline that cybersecurity incorporates both technical controls and human awareness, with staff training forming a critical line of defence.
What Can Be Done: Recommendations
For Critical Infrastructure Operators:
Implement true segmentation between IT and OT environments using firewalls and data diodes.
Adopt real-time ICS monitoring platforms such as those from Dragos or Nozomi Networks.
Conduct regular red team simulations that include physical compromise scenarios.
Update procurement standards to ensure vendor compliance with NIS2 and ISO/IEC 62443.
For Public Sector and Finance Authorities:
Strengthen identity verification using digital ID, e.g., GOV.UK One Login (currently in beta).
Deploy adaptive authentication and biometric MFA for citizen portals.
Expand public awareness campaigns to include phishing simulations and alerts.
Conduct tabletop crisis scenarios across departments to rehearse responses.
Conclusion: The Digital Border Is Everywhere
From the silent hum of a Norwegian dam to the bustling databases of the UK’s tax authority, modern societies are riddled with interconnected systems—each a potential target. What these two incidents show is that no sector is immune, and resilience is only as strong as the weakest link—be that a SCADA switch or an unsuspecting taxpayer.
Both governments are now under pressure to act decisively. The question is whether the broader digital ecosystem will learn from these cracks, or simply wait for the next fracture.