Why OT Visibility Is Now Critical
NCSC guidance signals a major shift. OT visibility is now the foundation of safety and resilience.
Operational Technology has quietly become one of the UK’s biggest sources of systemic risk. It runs cranes, batching plants, conveyor systems, logistics hubs, robotic lines, industrial sensors, PLCs and SCADA platforms. It is also the ideal target for a threat actor who wants maximum disruption for minimum effort.
The National Cyber Security Centre’s new 2025 guidance on maintaining a definitive view of OT architecture is the clearest signal yet that the era of “trusting legacy isolation” is over. Modern OT is connected, exposed and increasingly targeted. The organisations that thrive over the next decade will be those that can actually see their OT environments and govern them with the same rigour applied to finance, safety and operations.
This article breaks down what the NCSC advises, why it matters specifically for Construction, Manufacturing and Distribution, and the practical steps that leaders should prioritise.
Why it matters
Companies in these sectors face rising ransomware, supply-chain attacks and exploitation of legacy OT equipment. Most OT environments were never designed for today’s connectivity or adversaries. OT visibility is the foundation for safety, reliability and business continuity.
The Core Message from NCSC
The UK NCSC guidance says something deceptively simple:
No organisation can defend what it cannot see.
The way to fix this is to build and maintain a definitive record of your OT architecture: a single, validated, continually updated source of truth capturing assets, configurations, connectivity, information flows and third-party access.
This is not optional hygiene. It is the prerequisite for every meaningful control in OT security. It is how you stop an attacker pivoting unseen. It is how you avoid a “blind rebuild” after a ransomware incident. And it is how the board gains a real picture of operational exposure.
Why Construction, Manufacturing and Distribution Need This More Than Anyone
1. High reliance on long-life, legacy, safety-critical OT
Construction uses decades-old plant control systems in joint ventures and temporary works. Manufacturing lines run 24/7 with PLCs and HMIs installed before the cloud existed. Distribution facilities depend on automated conveyors, sortation systems and robotic pickers that rarely get patched.
Legacy equipment cannot absorb modern scanning, cannot authenticate strongly, and often uses insecure protocols by design. A single undocumented device becomes a perfect attack pivot.
2. Increasing third-party access
OEMs, integrators, BMS providers, machine vendors and maintenance specialists all require access. Many bring unmanaged 4G modems, remote support tools or unmonitored laptops. Third-party access is one of the NCSC’s top risk themes.
3. Multi-site, multi-vendor, multi-decade sprawl
Manufacturers and distributors inherit environments after M&A, plant expansions, ERP modernisation, cloud adoption or outsourcing. Construction projects involve temporary, fragmented digital estates with hundreds of contractors.
The result is architectural drift: everything works… until it doesn’t.
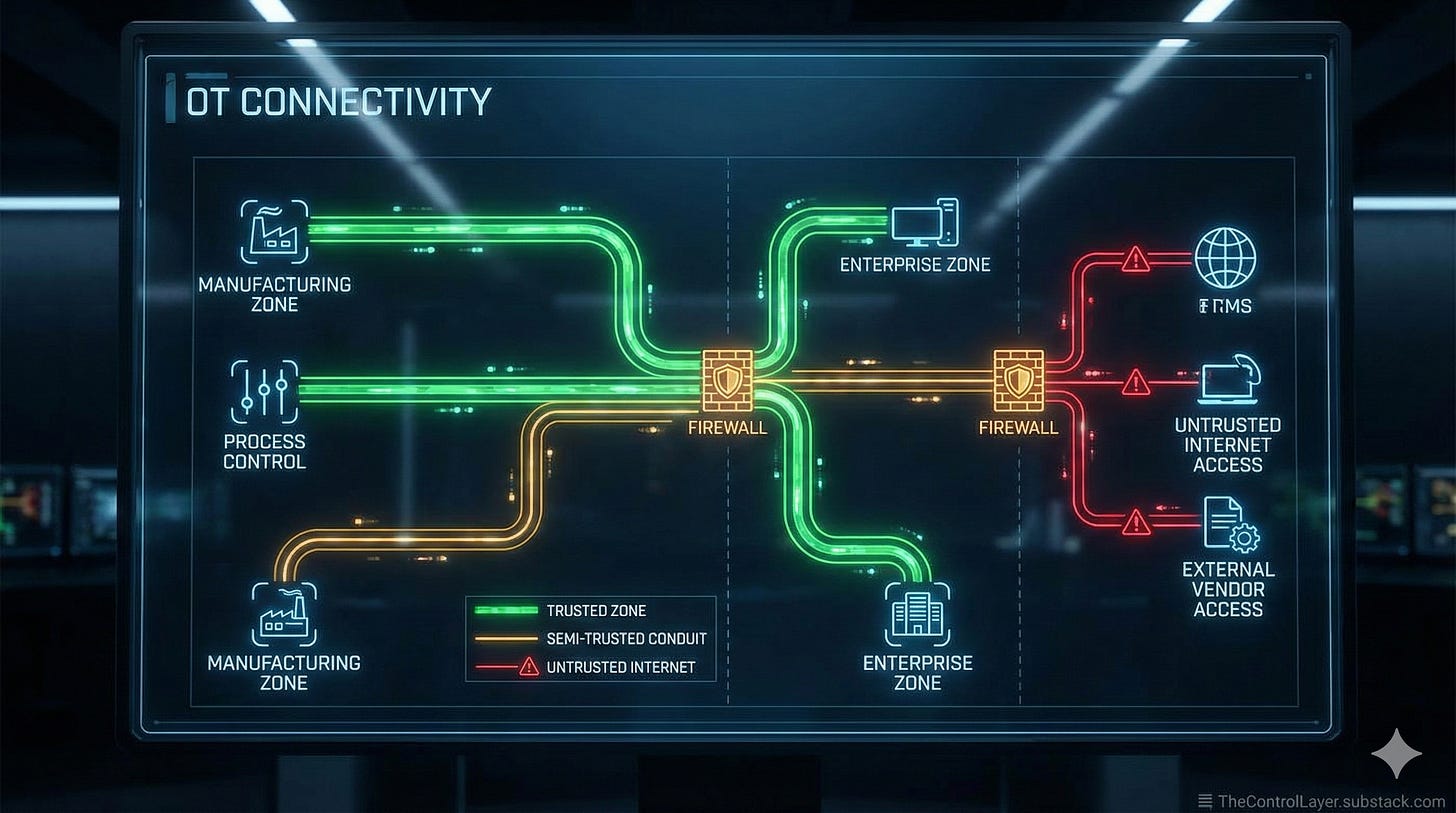
4. OT is now connected whether you intended it or not
Even if your leadership believes systems are “air-gapped”, they rarely are. According to the NCSC, modern OT routinely connects to business networks, cloud services and supplier platforms.
Connectivity that is undocumented is connectivity that an attacker can exploit.
5. Attackers are shifting from stealth to speed
Recent ransomware campaigns focus on fast exploitation of identity, remote access routes and OT-IT bridges. Without a clear map of your architecture, the blast radius is unknown.
Key Advice from the NCSC – Explained for Your Sector
Below is the NCSC’s guidance translated into sector-specific priorities.
1. Build a definitive OT record and keep it up to date
The NCSC calls this a single, validated record of OT architecture: assets, configurations, network flows, dependencies, protocols and connectivity.
For Construction and Manufacturing, this is your modern plant file.
For Distribution, it is your map of every conveyor, sorter, handheld terminal, PLC and IoT sensor.
Why it matters
It is the only way to understand cross-site risks.
It prevents shadow IT and undocumented vendor access.
It enables safe patching and maintenance planning.
It is essential for incident recovery.
2. Establish an OT information security management programme
This aligns to ISO 27001 and IEC 62443. It requires knowing what OT information you hold, how sensitive it is, who can access it, and how you secure it.
Why it matters
OT design files, remote access details, set points and credentials are gold to attackers.
Loss of integrity in engineering documents can cause unsafe configuration.
Loss of availability of design information can slow recovery by days.
Sector implications
Construction: Temporary works and site plant rely on documentation kept in multiple contractor systems.
Manufacturing: Process set points and logic files are often scattered across laptops and USBs.
Distribution: Warehouse automation vendors often hold copies of system configs without robust governance.
3. Categorise every OT asset by Criticality, Exposure and Availability
The NCSC emphasises evaluating assets based on:
Criticality (business, safety, security impact)
Exposure (discoverability and connectivity)
Availability (downtime tolerance and redundancy)
Why it matters
This is how you decide which devices get patched first, which get segmented, and where compensating controls are needed.
Sector implications
In manufacturing, outdated HMIs may have low criticality but very high exposure.
In distribution, SCADA servers are critical and highly exposed.
In construction, safety controllers must be highly available but have low exposure by design.
4. Document and justify every connection
The NCSC expects organisations to record:
What each asset communicates with
Why the connection exists
What protocols are used
Which ports are opened
Whether encryption, authentication and sanitisation are applied
Why it matters
Most attacks exploit undocumented routes, unmanaged vendor access or legacy protocols.
Sector implications
Distribution networks often expose OT through remote access for operations teams.
Manufacturing lines become vulnerable when IoT sensors or MES integrations bypass segmentation.
Construction site networks are temporary and routinely misconfigured, becoming attractive pivot points.
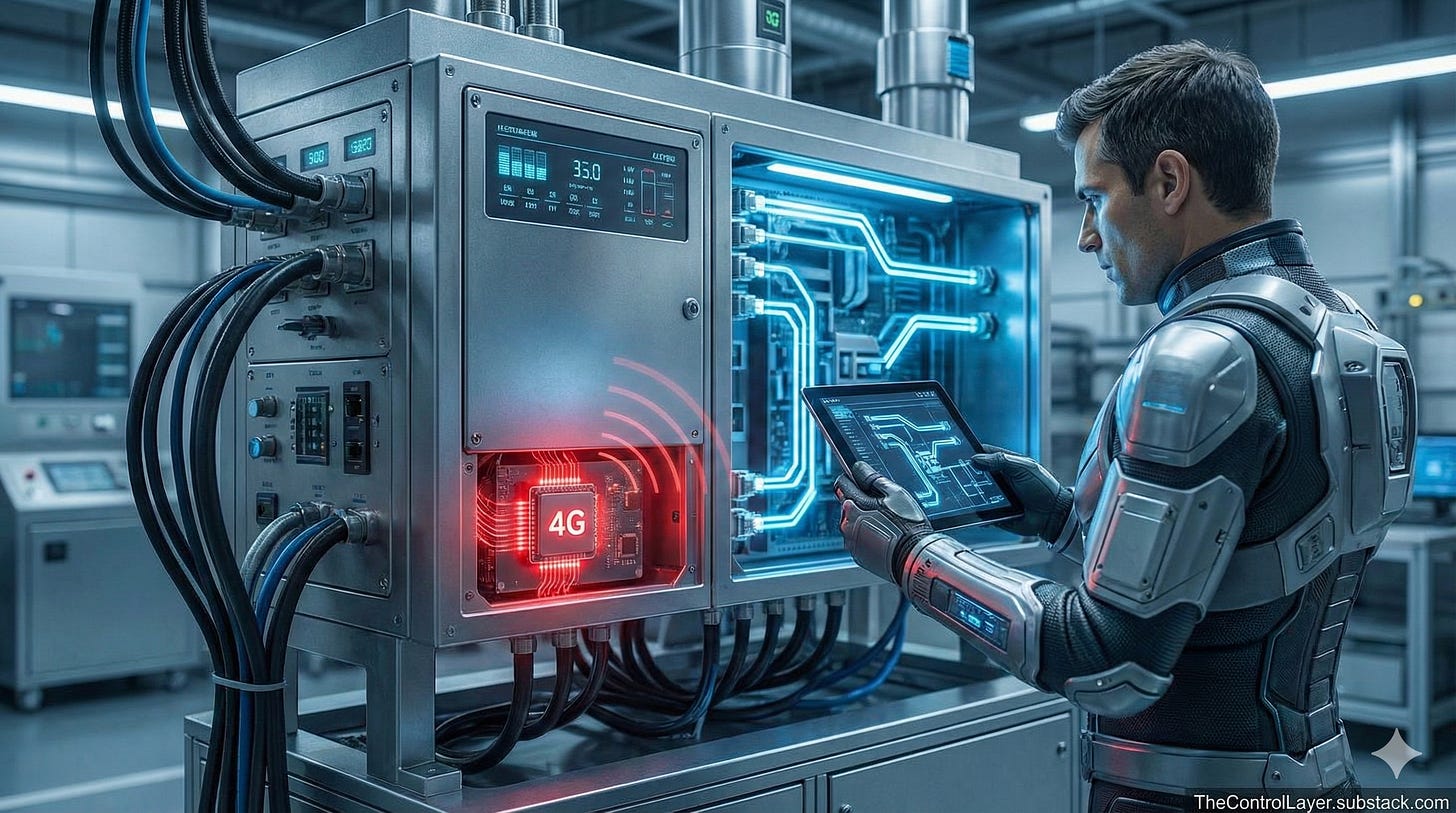
5. Understand and contain third-party risk
NCSC requires identifying:
Who is connecting
What trust level they have
What contractual access they demand
Whether any out-of-band channels exist (4G modems, Bluetooth, WiFi)
Why it matters
Third-party remote access is one of the most common initial access vectors for ransomware.
Sector implications
Construction: Plant vendors bring their own connectivity. Often undocumented.
Manufacturing: Robotics OEMs insist on continuous remote access.
Distribution: Automation providers deploy systems with hidden LTE modems for diagnostics.
Risks and Constraints
The biggest constraints in these sectors are:
• Legacy kit that cannot handle modern security controls
• 24/7 operations that prevent downtime
• Distributed estates across hundreds of sites and contractors
• Reliance on service providers who hold critical knowledge
• Poor visibility of older protocols such as Modbus, DNP3 or proprietary vendor interfaces
• High operational consequences where downtime means safety impact, lost production or disrupted supply chains
These constraints are real, but ignoring them creates systemic fragility. The guidance emphasises compensating controls, segmentation and careful design when modernisation is not possible.
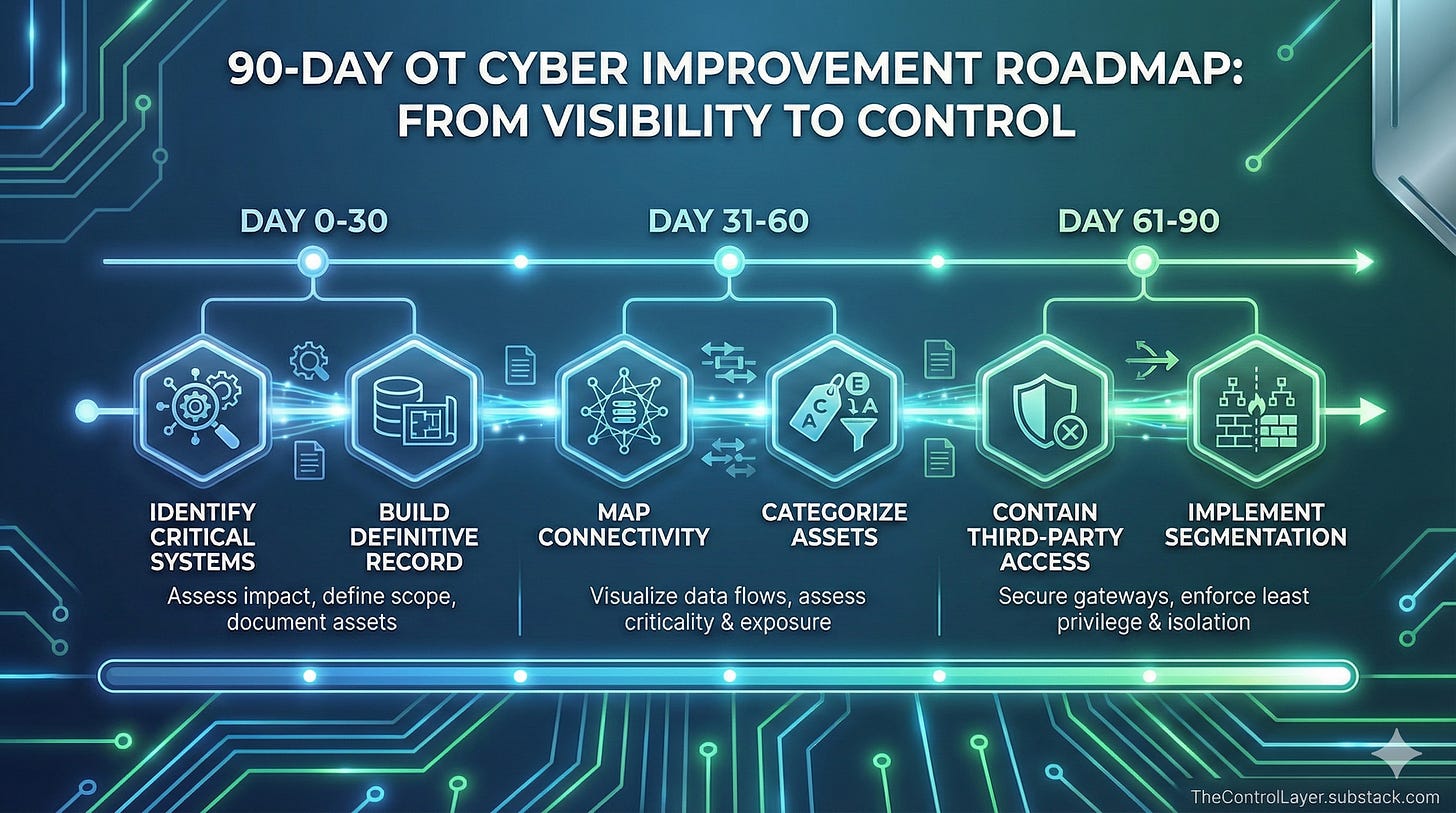
What to Do Next: A 90-Day Prioritised Plan
Identify your critical OT systems
Start with sites, lines or assets where failure impacts safety or production.
Build your first definitive OT record
Use existing documentation, SMEs, passive monitoring and vendor files to build an initial artefact.
Document all external connectivity
Uncover every modem, cloud integration and vendor tunnel.
Categorise assets by criticality, exposure and availability
Use this to inform a rational patching and segmentation plan.
Implement immediate containment
Remove unused connections, enforce MFA for remote access and apply read-only firewalls for untrusted protocols.
Begin third-party governance
Renegotiate contracts to reduce always-on access. Enforce monitored, just-in-time access.
Prepare for brownfield challenges
Invest in monitoring, protocol inspection and compensating controls.
This is the foundation of a long-term industrial cybersecurity programme aligned to NCSC, ISO 27001 and IEC 62443.
References
NCSC. “Maintaining a definitive view of your OT Architecture”. 2025.