Unmasking the Digital Threat: The Real Cyber Risks Facing the Construction Sector in 2025
As Britain’s construction sector powers the nation’s critical infrastructure—from water and energy to defence and healthcare—cyber threats have quietly escalated into a crisis demanding C-suite attention. Executive leaders at the country’s largest contractors, now face a rapidly evolving threat landscape shaped by ransomware gangs, state-sponsored hackers, and supply chain vulnerabilities. In this in-depth exploration, we unpack the real risks for construction organizations in 2025 based on only verified, trusted data, and offer practical visuals to illuminate the hidden dangers behind the digital curtain.
Construction Under Siege—The 2025 Cyber Threat Landscape
The UK construction sector has joined the ranks of the most targeted industries for cybercrime. In the government’s 2025 Cyber Security Breaches Survey, 43% of UK businesses reported experiencing a cyber incident in the preceding year. Construction firms, by virtue of their expansive digital ecosystems and pivotal role in national infrastructure, are squarely in attackers’ crosshairs.
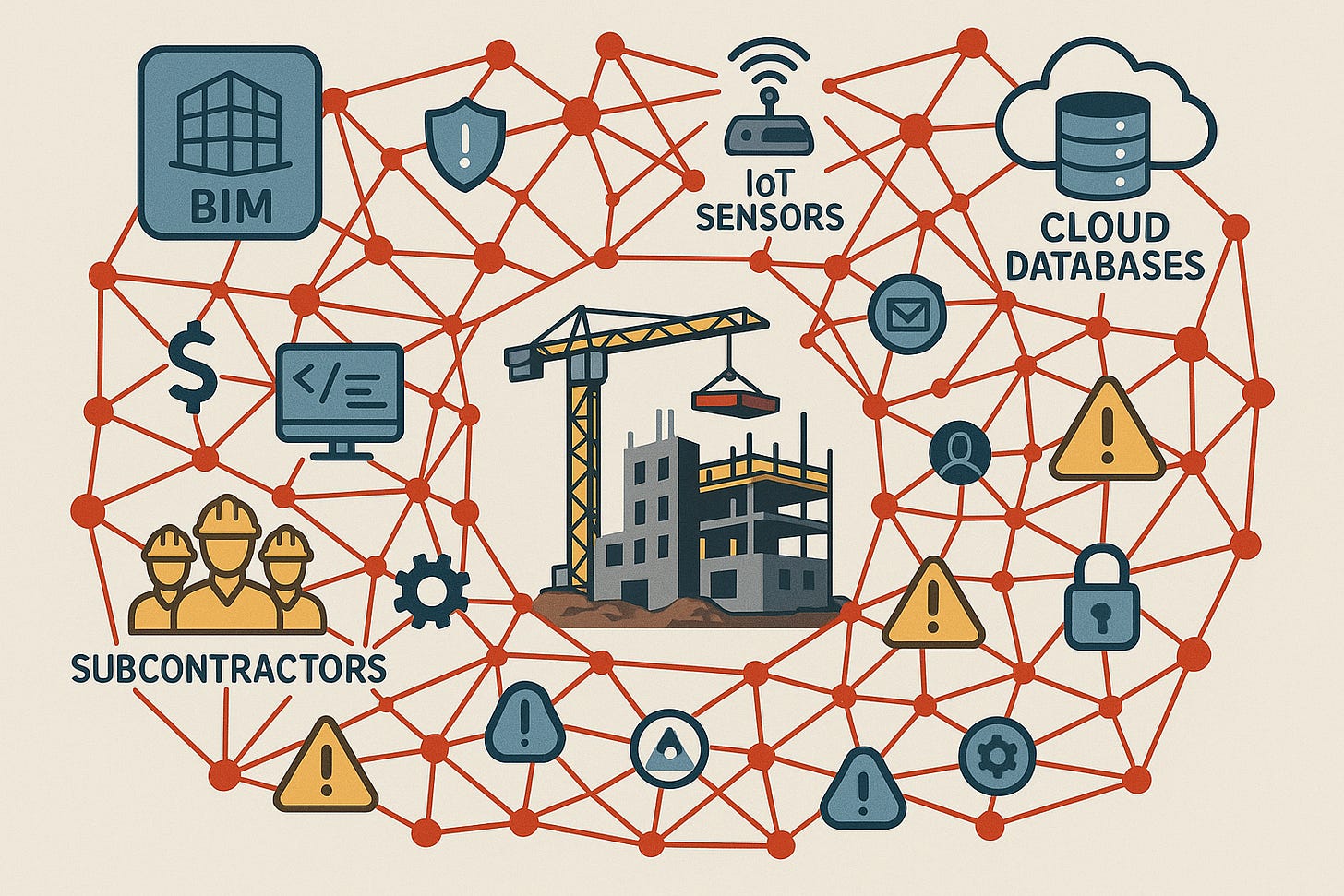
Why Construction Companies Are Prime Targets
Complex, Fragmented Supply Chains: Construction projects involve dozens (often hundreds) of subcontractors, vendors, and partners, creating a broad attack surface.
Reliance on Digital Tools: Project management systems, Building Information Modeling (BIM), cloud file storage, and IoT-powered equipment are now commonplace, multiplying digital entry points.
Critical Sector Interdependence: Many Tier 1 contractors are involved in delivering defence, water, energy, and healthcare projects; service disruption impacts millions.
The stakes are high: In 2024 alone, over 480 construction organisations globally were listed on ransomware data-leak sites, marking a 41% rise from the previous year.
Ransomware—The Sword of Damocles
Ransomware remains the industry’s most disruptive threat. In the first half of 2025, ransomware attacks across the UK surged, with the construction sector showing a pronounced upward trend. Median global ransom demands reached $5.37 million (£4.24 million).
Key Threat Facts:
35.5% of all 2024 breaches in the UK were directly tied to third-party supply chain incidents, a 6.5% increase over 2023.
Ransomware groups such as Qilin, Akira, and Clop are the most prolific, accounting for hundreds of incidents each.
How Ransomware Disables Construction Firms
Freezes project data, designs, and schedules
Compromises contract bids and sensitive client information
Halts site management systems, delaying multi-million pound projects
According to the National Cyber Security Centre (NCSC), sectors like construction face “a unique concentration of highly targeted, high-impact attacks”—a statement echoed in the NCSC’s first-ever industry guidance released in 2022.
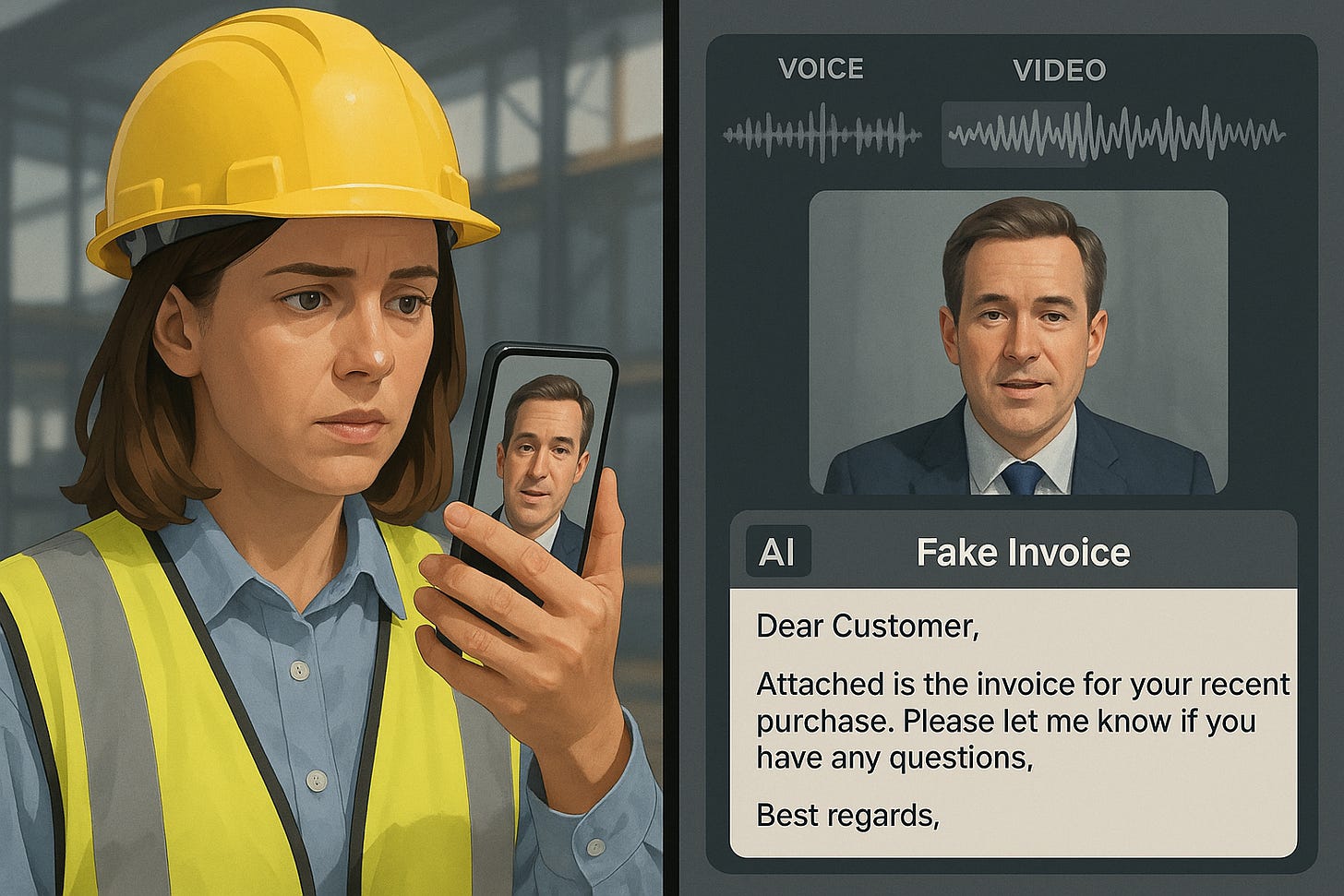
The Rise of AI-Powered Cybercrime
Criminals are wielding generative AI to launch more convincing phishing attacks and executive impersonations than ever before. The past year saw:
Over 200% increase in mentions of malicious AI tools on cybercrime forums.
AI-powered phishing emails now accounting for up to 40% of attacks targeting UK businesses.
Recent advances include:
Deepfake audio and video impersonations of executives and suppliers.
Automated spear-phishing campaigns that adapt messages in real time for maximum credibility.
Threat researchers warn that AI-powered attacks are lowering the technical barrier for attackers, making it easier for less skilled hackers to execute advanced campaigns.
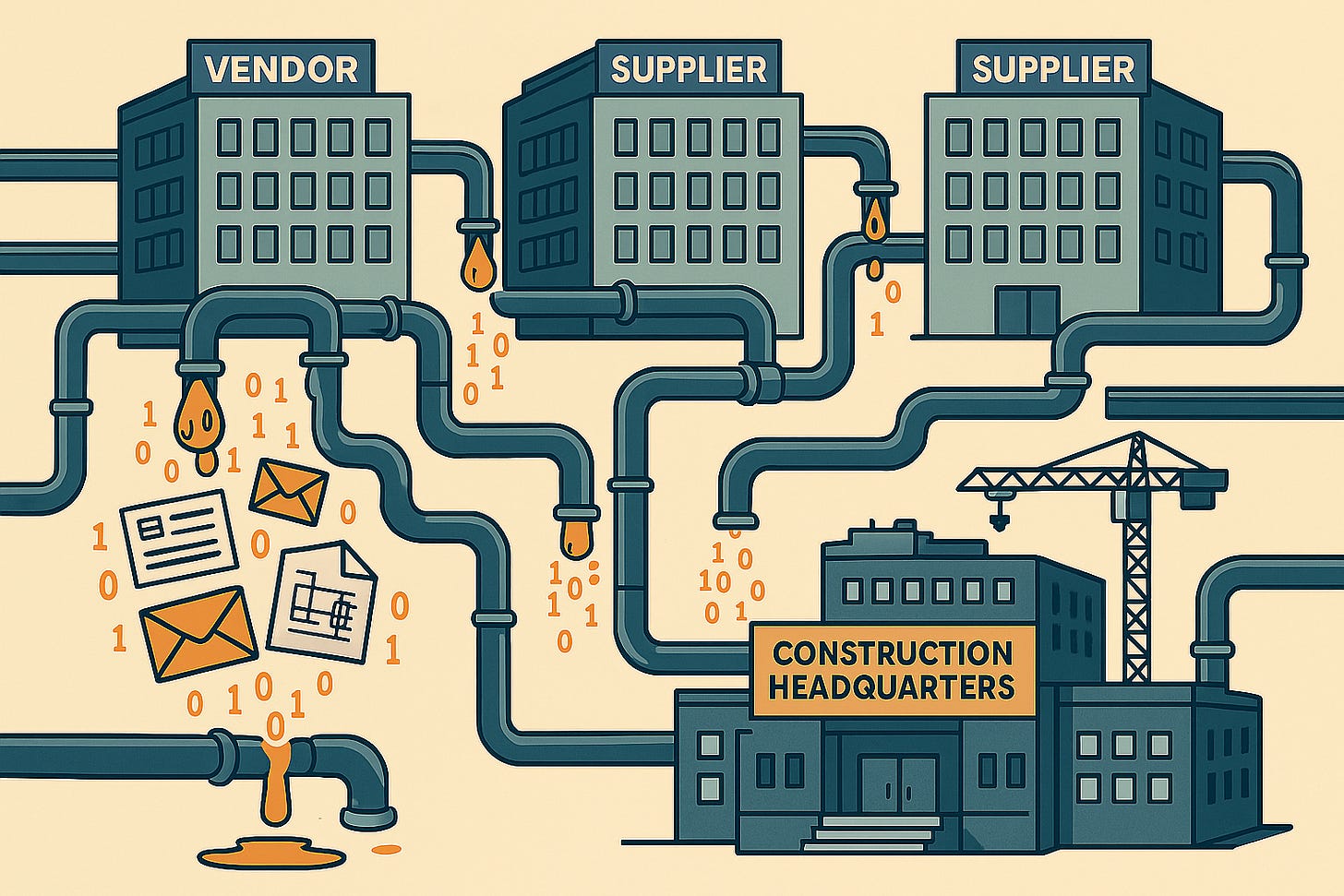
Supply Chain—The Silent Entryway
Construction’s heavy reliance on third-party vendors is a double-edged sword. While subcontractors and tech suppliers drive operational efficiency, their security gaps are frequently leveraged as entry points for major breaches.
Nearly one-third of all UK breaches originate from partner or vendor networks.
In 2024, nearly every major contractor had at least one integration with a third-party that had previously been breached.
Key supply chain threats include:
Compromised architectural or engineering firms providing tainted designs and plans
Infected software updates from equipment manufacturers
Unauthorised access through shared project management tools
This reality led the UK government to outline compulsory cyber risk assessments and enhanced reporting for critical sector supply chains in the Cyber Security and Resilience Bill.
Sector Spotlights—Unique Threats in Defence, Utilities, and Beyond
Sectors vital to national security each faces distinct but overlapping threats.
1. Defence
Adoption of Cyber Security Model Version 4 (CSMv4) by the Ministry of Defence is mandatory.
State-backed attackers, especially from Russia and China, are aggressively targeting defence projects and contractor networks.
2. Water & Energy
The water sector in 2024 faced at least six confirmed cyber incidents affecting drinking water, per government reports.
Cyberattacks on European energy infrastructure more than doubled between 2020 and 2022.
Programmable Logic Controllers (PLCs) and SCADA systems common across Industrial and Building systems remain prime vulnerabilities; failures can lead to service disruptions or even water contamination.
3. Healthcare Construction
Hospitals hit by ransomware in 2025 included University College London Hospitals, with attackers disrupting clinical systems and patient data access.
NHS suppliers are a major new target for extortion and data theft, as cybercriminals seek to exploit less secure entry points.
4. Transport Infrastructure
High-profile ransomware attack on Transport for London cost over £30 million and exposed thousands of customer accounts.
Railway Wi-Fi networks remain at risk, with attackers disrupting services at 19 stations in 2024.
5. Commercial Office Buildings
Building management systems, CCTV, and IoT devices have made commercial sites “SMART buildings” with doors left ajar.
Government survey data shows 27% of UK businesses reported cyber attacks targeting physical building systems in 2024—up steeply from the year before.
Building Information Modeling (BIM) and IoT—Dangers in the Details
BIM is now at the heart of nearly every major construction project. While essential for collaboration and efficiency, these digital "blueprints" dramatically multiply cyber risk.
Key vulnerabilities:
Detailed plans for critical sites (e.g., data centers, hospitals, substations) could be exfiltrated or manipulated, enabling physical or digital attacks.
Exploited BIM data can allow criminals to bypass physical security or sabotage safety systems.
IoT devices—from site cameras to smart cranes—often run on default credentials and are rarely updated..
Geopolitical Drivers—State Actors and Critical Infrastructure
Recent years have seen a sharp increase in attacks traced to state-sponsored actors operating with geopolitical intent:
NCSC managed over 200 nationally significant incidents since September 2024, a dramatic rise linked largely to the war in Ukraine and escalating China-West tensions.
Russian, Chinese, Iranian, and North Korean cyber-units actively probe UK infrastructure and contractors for espionage, sabotage, and future leverage.
The NCSC’s 2025 assessment places China as “the single biggest threat” to Britain’s critical infrastructure resilience—making major contractors a strategic target, not just an opportunistic one.
Regulatory Response—How the UK Government is Fighting Back
New Laws and Guidance
The forthcoming Cyber Security and Resilience Bill mandates cyber risk assessments and incident reporting for all suppliers in critical sectors.
MOD requirements (DEFCON 658) are now compulsory for any contractor on defence projects, raising barriers to entry for those unable to prove robust security.
The NCSC’s ground-breaking construction sector guidance frames cybersecurity as non-negotiable—“as essential as wearing a hard hat on site”.
Fines and contract suspensions are on the rise for non-compliance or breach-related disruptions.
Strategic Recommendations—Building a Cyber-Resilient Future
Immediate actions for leaders:
Enforce multi-factor authentication and least-privilege access across all systems
Rapidly phase out legacy platforms and enforce patching on all operational technology
Vet all suppliers against recognised cyber standards; terminate contracts with those who can’t provide current assurance certification
Institute AI-powered phishing simulation and staff resilience training
Segment Operational Technology (OT) from corporate IT networks
Sector-specific priorities:
Defence projects: Align 100% with MOD CSMv4 and DEFCON 658
Water/Energy: Secure PLC/SCADA environments, test for “air-gap failures”
Healthcare: Lock down BIM file sharing and medical device connections
Commercial and transport: Regular pen-testing of building management systems
Conclusion
Cyber threats facing the UK construction sector and firms are no longer theoretical—they are frequent, severe, and evolving. Leadership must approach digital risk management with the same rigor as health and safety: through robust controls, vigilant culture, and partnership with government intelligence.
The price of failure is not just financial loss or project disruption, but cascading impacts on national security, public health, and societal trust. By moving decisively now, forward-thinking companies can set the standard for resilient, digital-first construction that builds not only structures, but safety and trust for the generations to come.
References
UK Government, Cyber Security Breaches Survey 2025
SecurityScorecard, 2025 Construction Industry Threat Report
Sophos, The State of Ransomware 2025
ReliaQuest Cybercrime Analysis 2025
National Cyber Security Centre, "Cyber Security for Construction Businesses," 2024
NCSC, Sector-Specific Threat Alerts 2025
Darktrace Intelligence Report, Spring 2025
Proofpoint, Phishing and AI Threats 2025
UK Parliament, Cyber Security and Resilience Bill 2025
MOD, Cyber Security Model (CSMv4) and DEFCON 658 Guidance
NCSC, Government Threat Intelligence Updates 2025
DEFRA, Water Sector Incident Disclosures 2024
European Union Agency for Cybersecurity (ENISA), "Energy Sector Threat Review," 2025
NCSC Water Sector Security Guidance 2025
NHS, Major Cyber Incidents Register 2025
BBC News, "TfL Faces Record Cyber Ransom," April 2025
UK Govt, Business Cyber Survey 2024
Cambridge Centre for Smart Infrastructure, "BIM Security and the UK Built Environment," 2025
ENISA, IoT Security Status Report 2025