The UK's Cyber Reality Check
204 Incidents, and a Government That Finally Admits the Problem
Why it matters: The NCSC handled 204 nationally significant cyber incidents in twelve months – a 130% increase on the previous year. The Cyber Security and Resilience Bill is now in committee stage, expanding obligations to data centres, managed service providers, and critical suppliers. If your organisation falls into any of those categories, the compliance clock has started.
— Get The Control Layer in your inbox — weekly insights on AI, cybersecurity, and digital transformation: TheControlLayer.arkava.ai
The numbers nobody can ignore
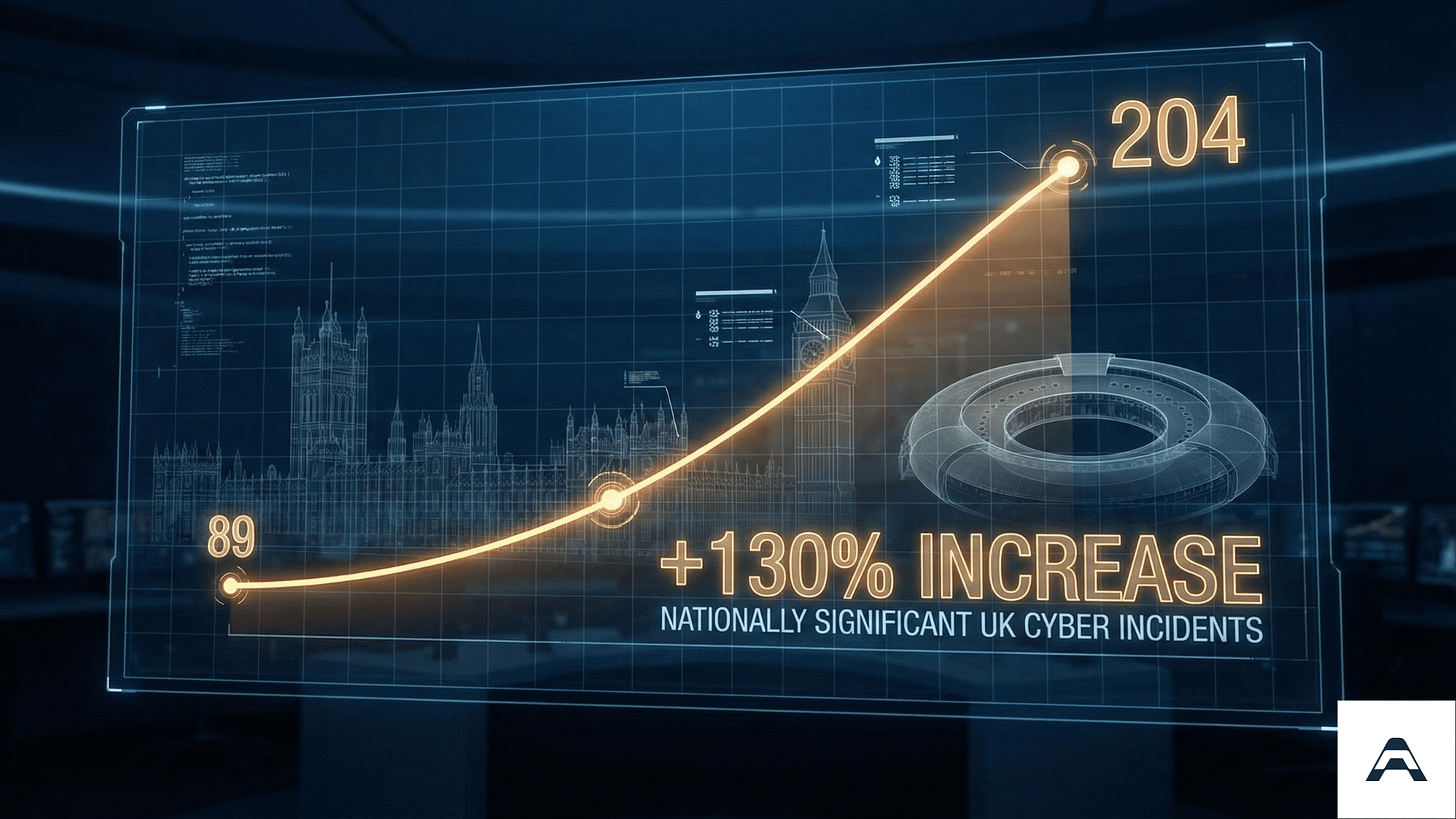
The NCSC Annual Review, published in October 2025, delivered the most candid official assessment of UK cyber readiness in a decade. The figures tell a story that even the most optimistic boardroom cannot dismiss: 204 nationally significant incidents between September 2024 and August 2025, compared with 89 the previous year [1]. Eighteen of those were classified as highly significant – a 50% increase from twelve the year before [1].
To put this in practical terms, the UK experienced an average of four nationally significant cyber attacks every week. Not minor probing. Not unsuccessful attempts caught at the perimeter. Incidents serious enough to warrant national-level coordination.
NCSC CEO Richard Horne described the situation with unusual directness, stating that cybersecurity is now a matter of business survival and national resilience [1]. GCHQ Director Anne Keast-Butler reinforced this by referencing the attacks on M&S, Co-op, and Jaguar Land Rover as a stark reminder of what happens when defences fail [1].
The 204-incident figure represents a 130% year-on-year increase in nationally significant cyber incidents. This is not a statistical anomaly – it reflects a structural escalation in threat capability and targeting.
Who is behind it, and how they operate
The NCSC assessment identifies China as the biggest state-level cyber threat to the United Kingdom [1]. However, the most immediate operational risk for mid-market organisations comes not from state actors directly, but from the ransomware ecosystem they have helped to professionalise.
The DragonForce group’s attacks on UK retail businesses demonstrated a pattern now familiar across threat intelligence reports: sophisticated initial access, lateral movement through poorly segmented networks, and double-extortion tactics combining data theft with encryption [1]. The rise of malware-as-a-service platforms has democratised access to these capabilities, meaning that threat actors with limited technical expertise can now deploy tools previously reserved for well-resourced groups [1].
For boards and security leaders, the implication is clear. The question is no longer whether your organisation is a target – at mid-market scale, you almost certainly are.
The question is whether your defences reflect the reality of 2026 threat operations or rather the assumptions of 2020.
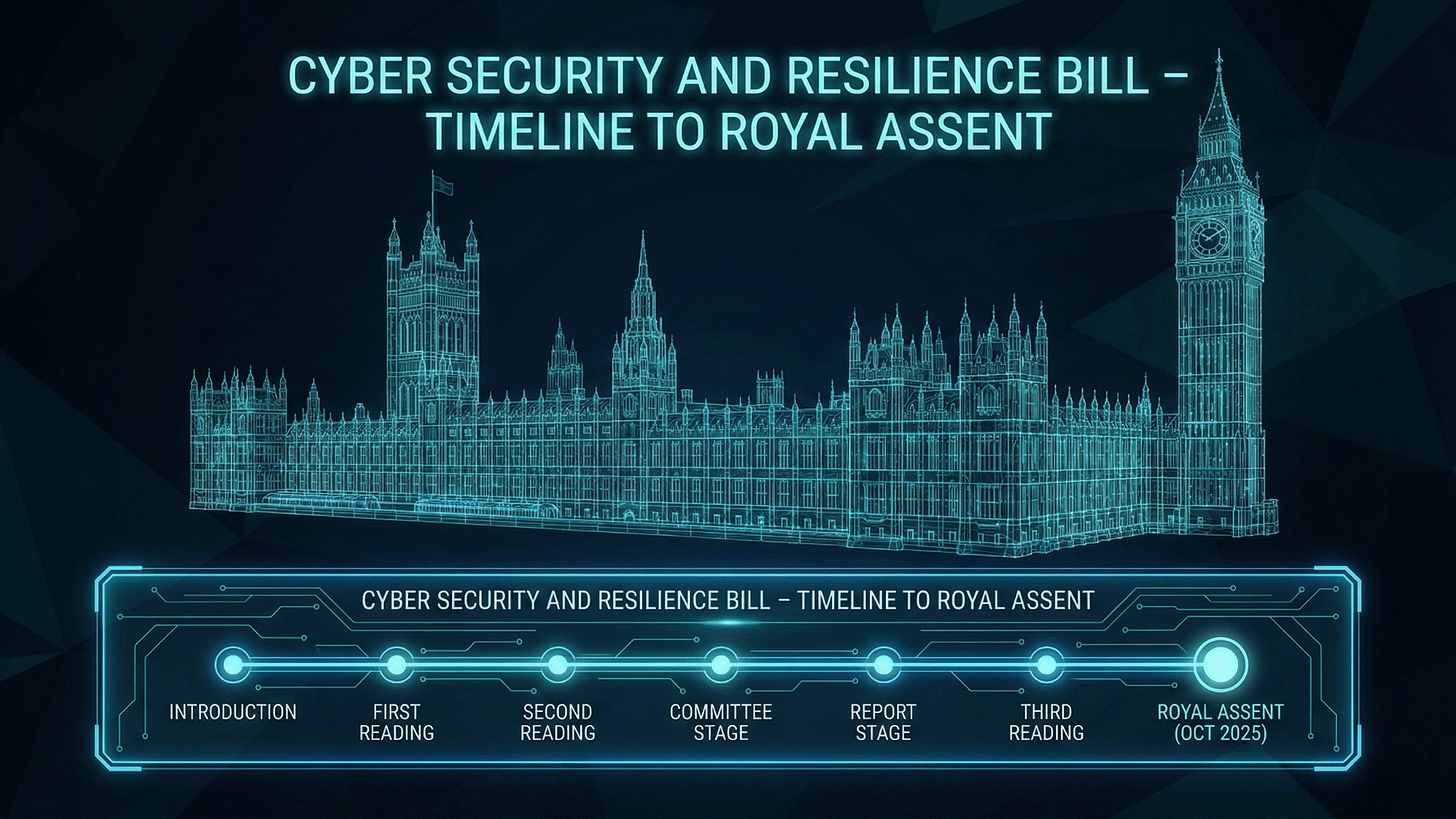
The legislative response: Cyber Security and Resilience Bill
The government’s response to this escalation is the Cyber Security and Resilience (Network and Information Systems) Bill, introduced on 12 November 2025 [2]. After its Second Reading on 6 January 2026, the Bill entered Public Bill Committee on 3 February 2026, with the committee expected to report by 5 March 2026 [2]. Royal Assent is anticipated by mid-2026.
This is not incremental policy refinement. The Bill significantly expands the scope of the existing NIS Regulations 2018 to include data centres, medium and large managed service providers, critical suppliers, and large load controllers [2]. If your organisation provides managed IT services to regulated sectors, or operates data centre infrastructure, you are moving from voluntary best practice to statutory obligation.
The Bill was announced in the King’s Speech 2024 as part of the government’s Plan for Change, signalling that cyber resilience is now treated as critical national infrastructure policy rather than a technology niche [2].
£210 million and a change in approach
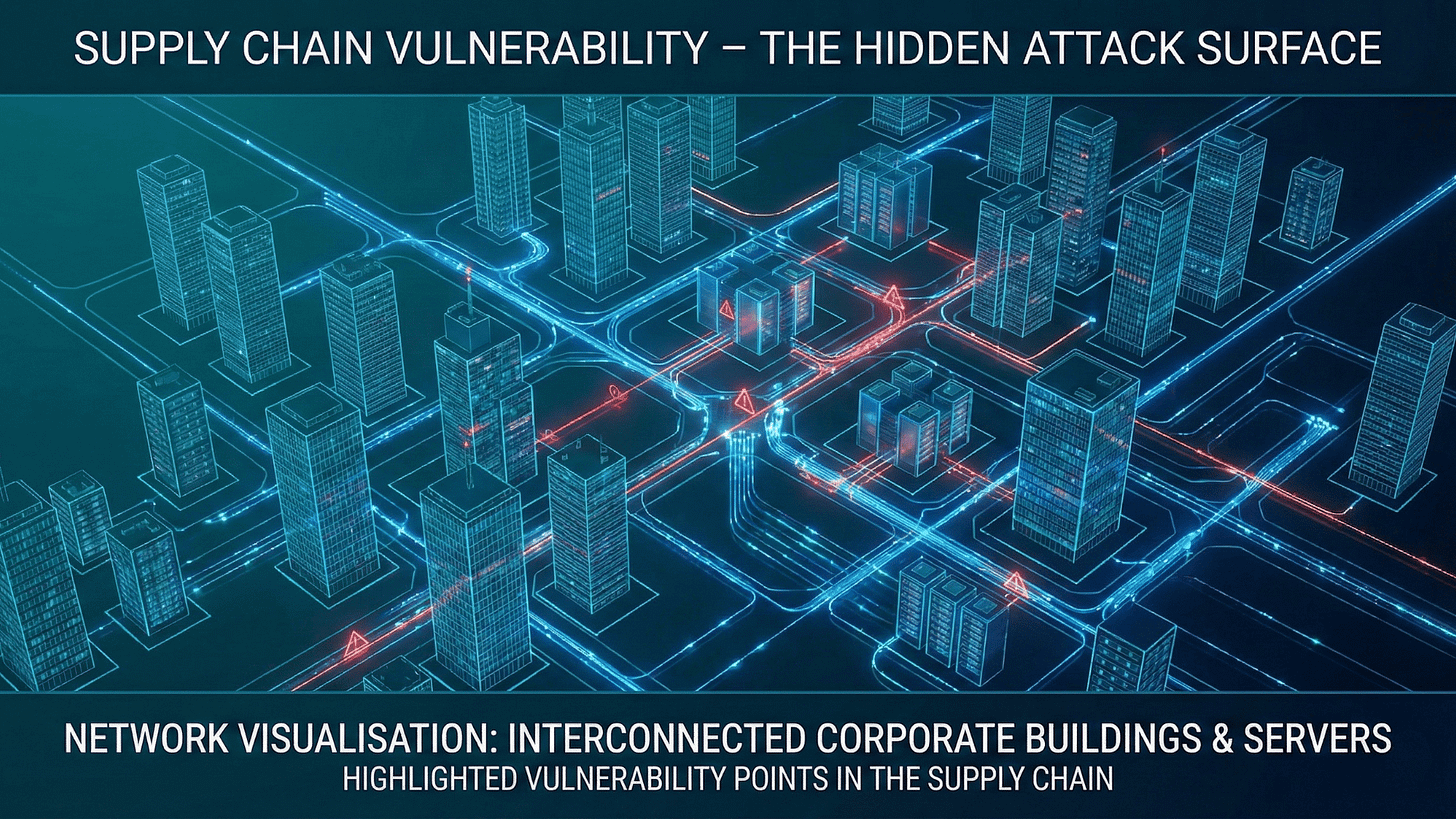
Alongside the Bill, the government published its Cyber Action Plan on 6 January 2026, committing £210 million to a new Government Cyber Unit that will centralise cross-government cyber risk management [3]. The plan introduces a Software Security Ambassador Scheme and a Software Security Code of Practice designed to address supply chain attacks – the vector responsible for some of the most damaging incidents in the NCSC’s review period [3].
The Cyber Profession initiative aims to tackle the talent pipeline problem that mid-market organisations know intimately. When you cannot compete with City salaries or government security clearance pathways, retaining cyber professionals becomes an existential challenge for organisations in the £50M–£500M revenue band.
Analysis
Here is what concerns me about these developments, and it is not the headline number.
The 204 incidents occurred during a period when most organisations believed they were improving their security posture. Spending on cyber tools has increased year on year across UK business. Boardroom awareness has never been higher. And yet the incident curve moved sharply upward.
This suggests a structural mismatch between how organisations invest in cyber resilience and how threat actors actually operate. The investment goes into tools. The attacks exploit people, processes, and architectural decisions made five years ago. You can buy the most sophisticated endpoint detection platform available and still fall to a compromised managed service provider in your supply chain – which is precisely the gap the new Bill attempts to close.
The timing of the Bill’s committee stage is significant. Organisations that wait for Royal Assent to begin compliance preparation will find themselves scrambling. Those that start now – mapping their supply chain exposure, auditing managed service provider contracts, assessing data centre dependencies – will be better positioned both for compliance and for genuine resilience.
Risks and Constraints
The 130% increase in nationally significant incidents deserves context. The NCSC also handled 429 total incidents, virtually unchanged from 430 the previous year [1]. This suggests the severity of incidents escalated significantly while overall volume remained stable. The increase in nationally significant classification may partly reflect changes in triage methodology and reporting thresholds, not solely an increase in attack volume.
The Cyber Security and Resilience Bill is still in committee. Amendments may alter scope, timelines, and enforcement mechanisms before Royal Assent. Organisations should prepare for the direction of travel without over-investing in specific compliance interpretations that may shift.
The £210M Cyber Action Plan investment, while substantial, is distributed across government. Its impact on private-sector mid-market organisations will be indirect, primarily through improved threat intelligence sharing and supply chain standards.
What to Do Next
For boards and executives: Request a board-level briefing on the NCSC Annual Review findings and the Cyber Security and Resilience Bill’s scope. Specifically ask whether your organisation or any of your critical suppliers fall within the expanded NIS regulations. This is a governance question, not a technology question.
For technical leaders: Map your managed service provider and data centre dependencies against the Bill’s expanded scope. Begin supply chain risk assessments now – contractual renegotiations take months, and you will want updated terms before enforcement begins.
For mid-market organisations: The window between now and Royal Assent (approximately mid-2026) is your preparation period. Commission an independent assessment of your cyber resilience posture against the new requirements. The organisations that treat this period as a head start rather than a waiting period will spend less, disrupt operations less, and comply faster.
Disclaimer: This article represents analysis based on publicly available information as of February 2026. It does not constitute legal, financial, or professional advice.
If your organisation needs support assessing its exposure to the Cyber Security and Resilience Bill’s expanded requirements, Arkava helps mid-market enterprises turn cyber resilience investment into measurable business outcomes.
References
[1] NCSC. “NCSC Annual Review 2025.” National Cyber Security Centre, 14 October 2025.
[2] UK Parliament. “Cyber Security and Resilience Bill.” Parliament.uk, 2025-2026.
[3] DSIT. “Cyber Action Plan.” Department for Science, Innovation and Technology, 6 January 2026.