The Sovereignty Calculation
What Switzerland's Palantir Rejection Teaches Every Democracy
Why it matters: Switzerland has formally rejected Palantir’s surveillance software after concluding that no operational benefit justifies losing control of national security data to a foreign government. The decision offers a template for how democracies can evaluate—and resist—technological dependencies that compromise their autonomy.
The Decision That Defied the Lobbying
In December 2024, Switzerland did something remarkable. After years of intensive courtship by one of the world’s most powerful data-analytics companies—including personal visits from Palantir’s chief executive, Alex Karp, and the opening of a Zurich office—Swiss defence officials said no [1].
The rejection followed a formal 20-page risk assessment by the Swiss Army, examining whether Palantir’s “Asset Readiness” platform was suitable for military intelligence operations. The conclusion was unambiguous: the risks to data sovereignty, privacy, and national security were too severe to justify adoption [1][4].
This was not a routine procurement decision. Palantir, the US-based company founded by Peter Thiel, specialises in integrating vast, fragmented datasets to identify patterns relevant to security and law enforcement. Its technology offers genuine tactical advantages—faster analysis, better pattern recognition, improved operational awareness [1]. Yet Switzerland calculated that these benefits came packaged with unacceptable strategic costs.
Why Data Sovereignty Matters More Than Efficiency
The core finding of the Swiss assessment concerned control; or rather, the permanent loss of it.
Because Palantir is incorporated in the United States and operates under US legal jurisdiction, Switzerland could not guarantee exclusive control over sensitive military data processed through the system [1][4]. The assessment warned that US intelligence agencies could legally access Swiss data under laws such as the Foreign Intelligence Surveillance Act (FISA) or Executive Order 12333, which permits signals intelligence collection from overseas targets [1].
The terms under which American authorities might access Swiss data are neither publicly disclosed nor contractually transparent [4]. In practice, this means Switzerland would be processing its most sensitive security information through infrastructure that another government could access—unilaterally and without Swiss consent.
For a constitutionally neutral nation, this is not merely a legal technicality. It is an existential question about who controls the data that shapes national security decisions.
The Swiss Army explicitly stated: “Palantir is a US-based company where there is a possibility that sensitive data could be accessed by the American government and intelligence agencies” [1].
The Hidden Costs of Convenience
Beyond immediate data-access concerns, the Swiss assessment identified structural dependencies that would compound over time [1][4].
Vendor lock-in emerged as a critical vulnerability. Palantir’s proprietary architecture and opaque algorithms would make switching to alternative systems extremely difficult and costly. Once adopted, the relationship becomes sticky and leverage shifts to the vendor [4].
Cost uncertainty added another layer of risk. Palantir publishes no price list. Long-term cost prediction is impossible, and the company holds significant negotiating power in contract renewals [1][4].
Staff dependency created organisational vulnerability. Operating the system requires specialists trained on Palantir’s proprietary tools, deepening institutional reliance on a single foreign provider [1].
Technical fragility raised operational concerns. Asset Readiness requires high-quality, real-time data streams; communication disruptions or signals-intelligence threats could degrade system performance precisely when it is needed most [4].
These dependencies accumulate. What begins as a tactical enhancement becomes a strategic constraint; limiting freedom of action and creating exposure in future crises.
The Privacy and Fairness Problem
The Swiss assessment also flagged concerns about what the technology does, not just who controls it [1][4].
Palantir’s architecture is designed to integrate previously fragmented datasets, creating unprecedented visibility into individuals’ relationships, movements, and associations. Whilst this capability can aid legitimate investigations, it also creates discriminatory potential. Algorithmic analysis based on correlations could lead to unintended targeting of individuals or groups; particularly those already subject to law-enforcement scrutiny [1][4].
Crucially, Palantir’s algorithms are proprietary. Swiss authorities could not independently verify the fairness or accuracy of analytical outputs [1]. This opacity conflicts with fundamental principles of democratic accountability: citizens subject to surveillance-derived decisions have a right to understand how those decisions are made.
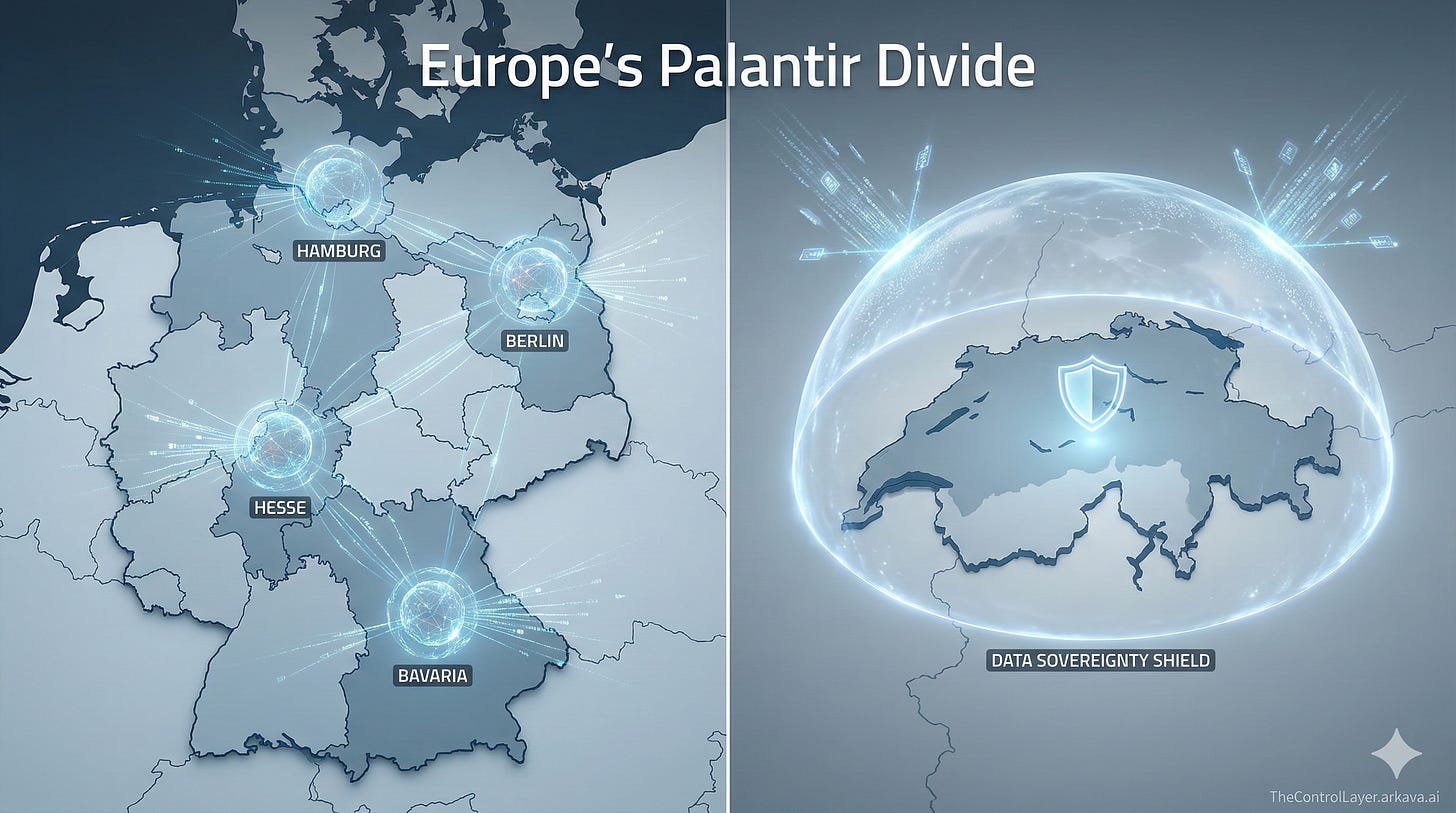
The European Divide
Switzerland’s rejection stands in sharp contrast to decisions elsewhere in Europe. Four German state police forces—in North Rhine-Westphalia, Hesse, Bavaria, and Baden-Württemberg—have adopted Palantir systems for criminal investigation and data analysis [3].
This divergence raises uncomfortable questions. Why did Switzerland prioritise sovereignty where Germany accepted dependency? Are German risk assessments equally rigorous, or do NATO alliance pressures and US security guarantees override independent analysis? How do German data-protection frameworks justify accepting risks that Swiss experts deemed unmanageable? [3]
German courts have already found predictive-policing tools which use Palantir-style analytics incompatible with rule of law [3]. Yet German Interior Minister Alexander Dobrindt has not publicly addressed these tensions and has declined to rule out expanding Palantir deployment to federal police forces [3].
The contrast illuminates a fault line in European technology governance. Some nations treat sovereignty as negotiable when operational convenience beckons. Others—Switzerland among them—treat it as a red line.
The Controversy Shadow
The timing of Switzerland’s decision carries additional weight. In September 2024, reports emerged linking Palantir technology to Israeli military operations, including data-analytics systems used in targeting decisions during the Gaza campaign. More recently, Palantir has been associated with Israel’s September 2024 pager attack in Lebanon, which killed at least 37 civilians and injured thousands [2][5].
Whilst Palantir has not directly confirmed involvement in these operations, the association intensified European concerns about the company’s role in conflicts and the potential for Swiss data to serve purposes contrary to Swiss neutrality [2][5].
For a nation whose constitution enshrines neutrality, using American surveillance infrastructure creates dependencies that could compromise that status in future international crises.
Risks and Constraints
Switzerland’s decision is not without trade-offs.
Capability gap: Rejecting Palantir leaves the Swiss military without an immediate replacement for integrated data analytics. Building alternatives takes time [1].
Investment required: Whether pursuing European commercial vendors, open-source platforms, or in-house development, each pathway requires significant resources and expertise [1].
Peer pressure: As NATO-aligned states adopt Palantir, Switzerland may face interoperability challenges or diplomatic friction in joint operations [3].
Uncertainty about alternatives: European vendors and open-source solutions are less battle-tested than Palantir’s platforms. Performance and reliability are not yet proven at equivalent scale [1].
These constraints are real. Switzerland’s calculation is that they are preferable to the structural dependencies and sovereignty risks that Palantir’s adoption would create.
What to Do Next
The Swiss assessment recommends three strategic directions—relevant not just for Switzerland, but for any government facing similar decisions [1]:
For national security leaders: Commission independent, rigorous technical assessments before adopting foreign surveillance platforms. The Swiss model—examining jurisdiction, data access, vendor lock-in, cost transparency, and algorithmic accountability—offers a replicable framework.
For procurement officials: Demand published pricing, transparent algorithms, and contractual guarantees against foreign government data access. Absence of these should be disqualifying.
For technology strategists: Invest in European commercial alternatives, open-source analytics platforms, and sovereign in-house development. Each option avoids the structural dependencies that proprietary US systems create.
For citizens and civil-society organisations: Advocate for transparency in government surveillance procurement. Decisions made behind closed doors—without public debate—undermine democratic accountability.
Disclaimer: This article represents analysis based on publicly available information as of December 2024. It does not constitute legal or procurement advice. Readers should conduct independent assessments appropriate to their jurisdiction and circumstances.