When Your Security Team Becomes the Threat
How Ransomware Gangs Are Recruiting Insiders
Why it matters: Ransomware gangs have industrialised insider recruitment, offering your IT staff 15–25% of ransom payments for administrative access. This transforms insider threat from theoretical edge case to primary attack vector — and most organisations' governance frameworks are unprepared.
Join The Control Layer for weekly perspectives on AI, cybersecurity, and building technology that serves human purpose.
The job offer your security engineer won’t mention
Somewhere in your organisation, someone with privileged access has received an interesting proposition. Not through a dark web forum or encrypted chat — but through LinkedIn, professional networks, or even direct email to their corporate inbox.
The pitch is straightforward: provide credentials, disable backup systems, or simply leave a door open. In return, receive a percentage of whatever ransom your employer eventually pays. Anonymous payment in cryptocurrency. No face-to-face meetings. Minimal risk of detection.
This is not hypothetical. In December 2025, BlackCat/ALPHV successfully recruited a cybersecurity professional — someone whose literal job was preventing exactly this kind of attack — to facilitate a breach. The individual received a reported 20% of the ransom payment.[1]
Welcome to the industrialisation of insider threat.
From opportunism to operating model
For years, insider threat occupied a peculiar position in enterprise risk registers: acknowledged as dangerous, yet treated as unpredictable. You might screen employees at hiring, monitor for anomalous behaviour, and hope that loyalty or fear of consequences would deter betrayal.
Ransomware-as-a-service gangs have rendered this approach obsolete.
NCC Group’s January 2026 analysis reveals that major RaaS operations — Qilin, Medusa, and the remnants of BlackCat/ALPHV — now run formalised recruitment programmes.[1] These are not ad-hoc approaches to disgruntled employees. They are structured affiliate expansion efforts with defined compensation models, anonymity guarantees, and target profiles.
The economics are compelling. A ransomware gang investing in zero-day exploitation, phishing infrastructure, and technical penetration might spend weeks or months establishing access to a target environment. An insider with administrative credentials can provide equivalent access in an afternoon. The cost-benefit calculation has shifted decisively toward human exploitation.
The uncomfortable truth: your perimeter defences assume the threat is outside. Insider recruitment programmes target people who are already inside your most sensitive systems.
Who they’re targeting — and why it matters for governance
The recruitment focus is disturbingly strategic. RaaS gangs are not approaching random employees; they are targeting specific roles with maximum leverage:
IT administrators and security engineers represent the primary target class. These individuals possess the technical knowledge to disable monitoring, create persistent access, and — critically — understand which actions will trigger alerts and which will not. The December 2025 BlackCat case demonstrates that even professionals whose identity is built around defending organisations can be compromised.[1]
HR and identity management staff control credential issuance, onboarding processes, and employee records. Access to these systems enables creation of ghost accounts, manipulation of access permissions, and — in more sophisticated scenarios — establishment of entirely fictitious employees with legitimate system access.
Backup operators and disaster recovery personnel hold the keys to organisational resilience. Ransomware is only effective if victims cannot restore from backups. An insider who degrades backup integrity before an attack transforms a recoverable incident into an existential crisis.
The pattern suggests reconnaissance. Threat actors are not casting wide nets; they are identifying specific individuals with specific capabilities, then making tailored approaches. This implies pre-attack research into organisational structures, likely through OSINT gathering from LinkedIn, corporate websites, and professional publications.
The compensation model: why your salary might not be enough
The financial incentives are substantial and deliberately calibrated. NCC Group documents offers ranging from 15–25% of eventual ransom payments, with cryptocurrency settlement and promised anonymity.[1]
Consider the arithmetic. A mid-market organisation facing a £2 million ransom demand — not unusual for companies in the £50–500 million revenue band — represents a potential £300,000–£500,000 payout for a cooperating insider. For an IT administrator earning £60,000 annually, this represents five to eight years of salary for a single act of betrayal.
The moral calculus is further complicated by rationalisation opportunities. Ransomware gangs explicitly position their recruitment as victimless: “The company has insurance. No one gets hurt. You’re just accelerating an inevitable outcome.” These narratives provide psychological cover for individuals who might otherwise resist.
This is not to suggest your teams are inherently untrustworthy. The vast majority of employees would never consider such offers. But governance cannot rely on universal virtue. It must assume that among any sufficiently large workforce, some individuals will face financial pressure, personal grievances, or moral flexibility that makes recruitment approaches viable.
Analysis: why traditional insider threat programmes fail
Most organisations’ insider threat controls were designed for a different problem — the disgruntled employee who acts alone, or the careless user who accidentally exposes data. These controls assume insider threats emerge from internal conditions: workplace conflict, personal crisis, or ideological motivation.
The RaaS recruitment model inverts this assumption. The threat originates externally, targeting individuals who may have no prior indicators of risk. Traditional behavioural monitoring looks for anomalies against baseline behaviour; a well-coached insider can maintain normal patterns until the moment of betrayal.
Three structural weaknesses emerge:
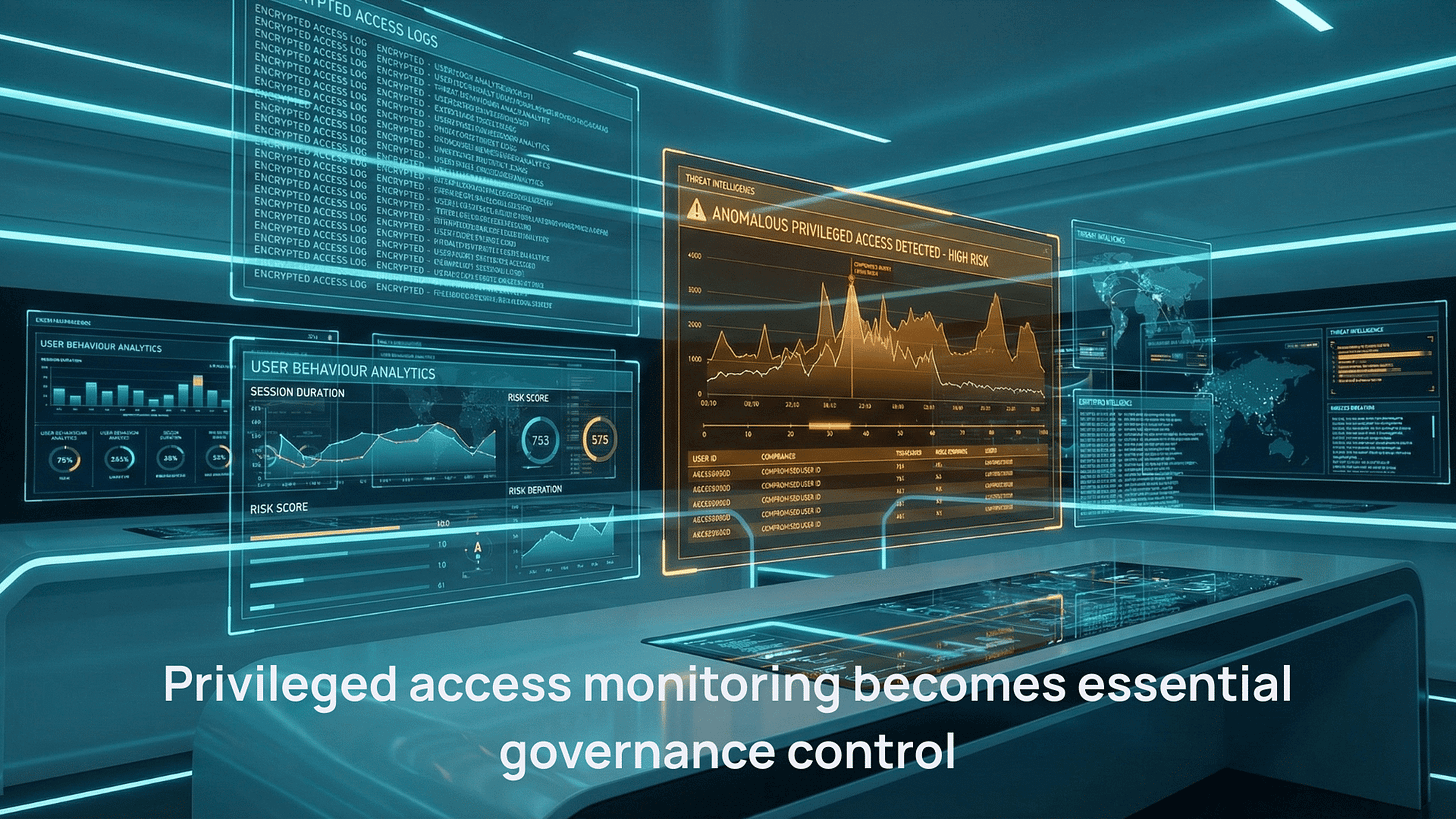
Privilege accumulation without accountability. Many organisations allow administrative credentials to persist indefinitely, with limited logging of privileged actions. An insider can conduct preparatory activities — disabling alerts, mapping backup systems, creating persistence mechanisms — over weeks or months without triggering review.
Backup systems as single points of failure. The same individuals responsible for backup operations often possess the access to compromise those backups. When the attacker is the backup administrator, the assumption that “we can always restore” becomes dangerously optimistic.
Trust-based access models. Enterprise security architectures frequently assume that authenticated users with appropriate role assignments should receive broad access within their functional domain. This model collapses when the authenticated user is cooperating with external threat actors.
Risks and constraints
Addressing insider recruitment requires acknowledging uncomfortable organisational realities.
Zero trust creates friction. Implementing genuine least-privilege access, continuous authentication, and comprehensive logging of privileged actions will slow operations. Users will complain. Productivity metrics may decline. Leadership must accept these trade-offs as the cost of resilience.
Monitoring has limits. Even sophisticated user behaviour analytics cannot reliably detect a well-coached insider acting within their authorised access patterns. Technical controls are necessary but insufficient; governance frameworks must assume some insider compromises will occur and design for containment.
Cultural implications are significant. Communicating to employees that the organisation is implementing enhanced monitoring because “we cannot fully trust anyone” requires careful handling. Poorly executed messaging can damage morale and, ironically, increase insider risk by eroding organisational loyalty.
Resource constraints are real. Mid-market organisations lack the security operations centre staffing to implement comprehensive privileged access monitoring. Solutions must be proportionate to organisational capacity — which often means accepting residual risk and focusing controls on highest-impact assets.
What to do next
The shift from opportunistic insider threat to industrialised recruitment demands corresponding evolution in governance and controls.
For boards and executives: Commission an independent assessment of privileged access governance. Ask specifically: who has administrative access to backup systems, and what oversight exists for their actions? Ensure cyber risk registers explicitly address insider recruitment as a threat vector, not merely “insider threat” as an abstract category. Consider whether director-level accountability for insider threat governance is adequately defined.
For security leaders: Implement privileged access management with just-in-time elevation and comprehensive session recording. Establish separation of duties for backup operations — no single individual should be able to both manage backups and delete backup logs. Deploy user and entity behaviour analytics focused on privileged account classes, accepting that detection rates will be imperfect. Conduct tabletop exercises specifically modelling insider-facilitated ransomware scenarios.
For mid-market organisations with limited resources: Focus controls on your crown jewels. Identify the three to five systems whose compromise would be existential, and implement disproportionate monitoring and access controls for those specific assets. Consider managed detection and response services that provide 24/7 privileged access monitoring without requiring internal SOC staffing. Ensure backup systems include immutable storage that cannot be modified even by backup administrators.
For HR and people functions: Review pre-employment screening for roles with privileged access, recognising that past behaviour is an imperfect predictor of future compromise. Establish confidential reporting channels for employees who receive suspicious approaches. Consider whether exit procedures adequately address credential revocation and knowledge transfer risks.
Disclaimer: This article represents analysis based on publicly available information as of January 2026. It does not constitute legal, financial, or professional advice.
If your organisation needs support implementing insider threat governance frameworks, Arkava helps mid-market enterprises turn security investment into measurable risk reduction.
References
[1] NCC Group. “Ransomware Report: December 2025.” January 2026.
[2] National Cyber Security Centre (NCSC). “NCSC Annual Review 2025.” October 2025.
[5] S-RM Cyber Intelligence. “ShinyHunters Launch Vishing Attacks on SSO Accounts.” 30 January 2026.
[6] Acumency Cyber. “Cyber Threat Intelligence Digest – January 2026: Week 4.” 31 December 2025.