When the Wind Farms Went Dark
What Poland's Grid Attack Means for UK Energy
Why it matters: Late last year, Russian state actors deployed wiper malware across 30 Polish wind, solar, and combined heat and power facilities — the first documented destructive cyberattack on distributed renewable energy resources. Operators lost command and control of their systems during an extreme cold period. If your organisation operates, supplies, or depends on distributed energy infrastructure, the defence model you rely on was just proven inadequate.
The attack nobody expected
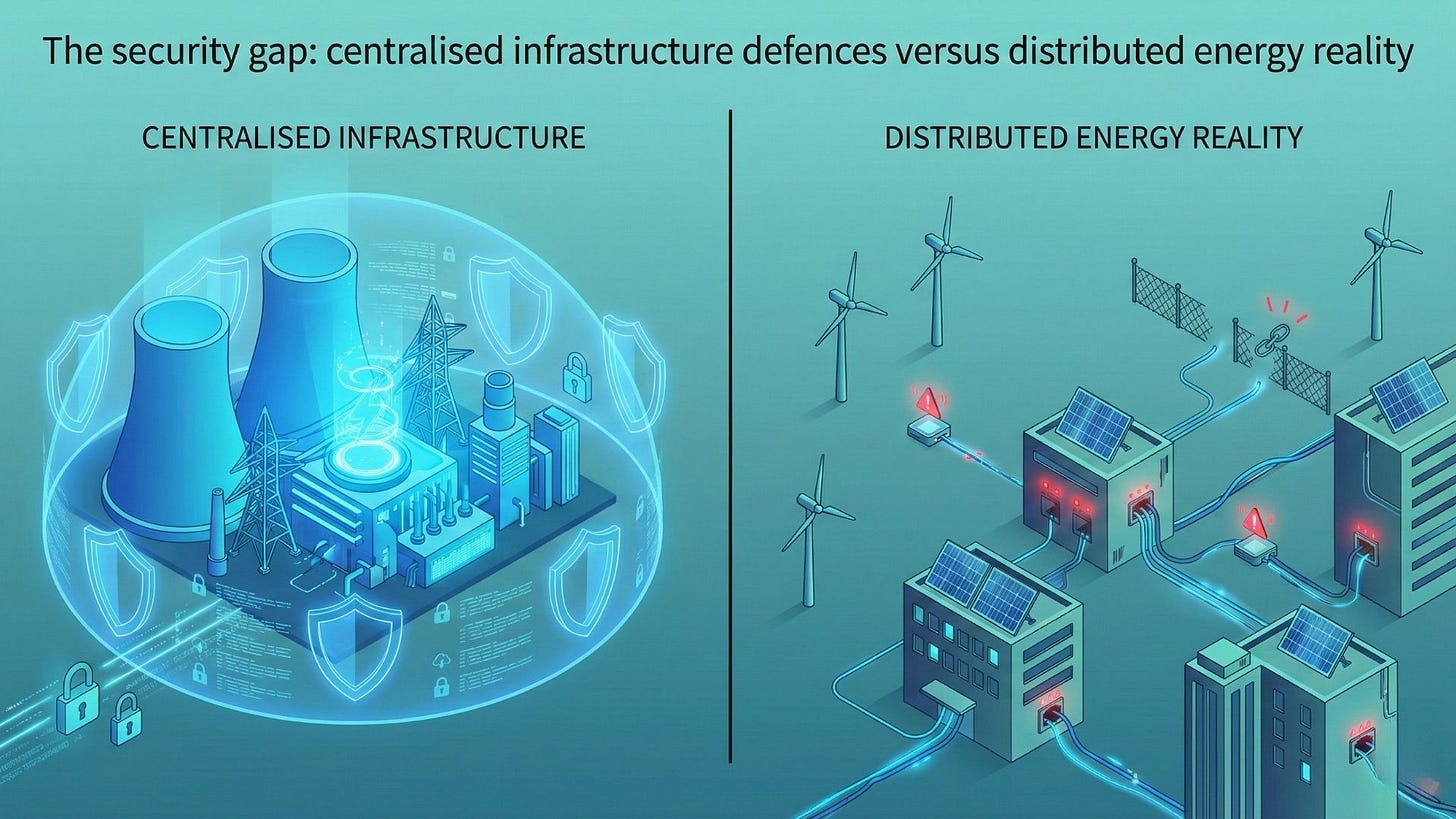
For a decade, the energy sector’s cybersecurity playbook was written around centralised power stations. Ukraine’s grid attacks in 2015 and 2016 targeted transmission-level infrastructure — large, visible, and (eventually) defensible. Poland’s incident rewrites the threat model entirely.
In late December 2025, attackers attributed to Berserk Bear (Russian FSB) and Sandworm (Russian GRU) compromised 30 distributed energy resource (DER) facilities across Poland. Initial access came through unpatched FortiGate edge devices without multi-factor authentication, using reused credentials. Once inside, they moved laterally through operational technology (OT) networks exploiting devices running default login credentials — the digital equivalent of leaving every door unlocked with the key under the mat [1][2].
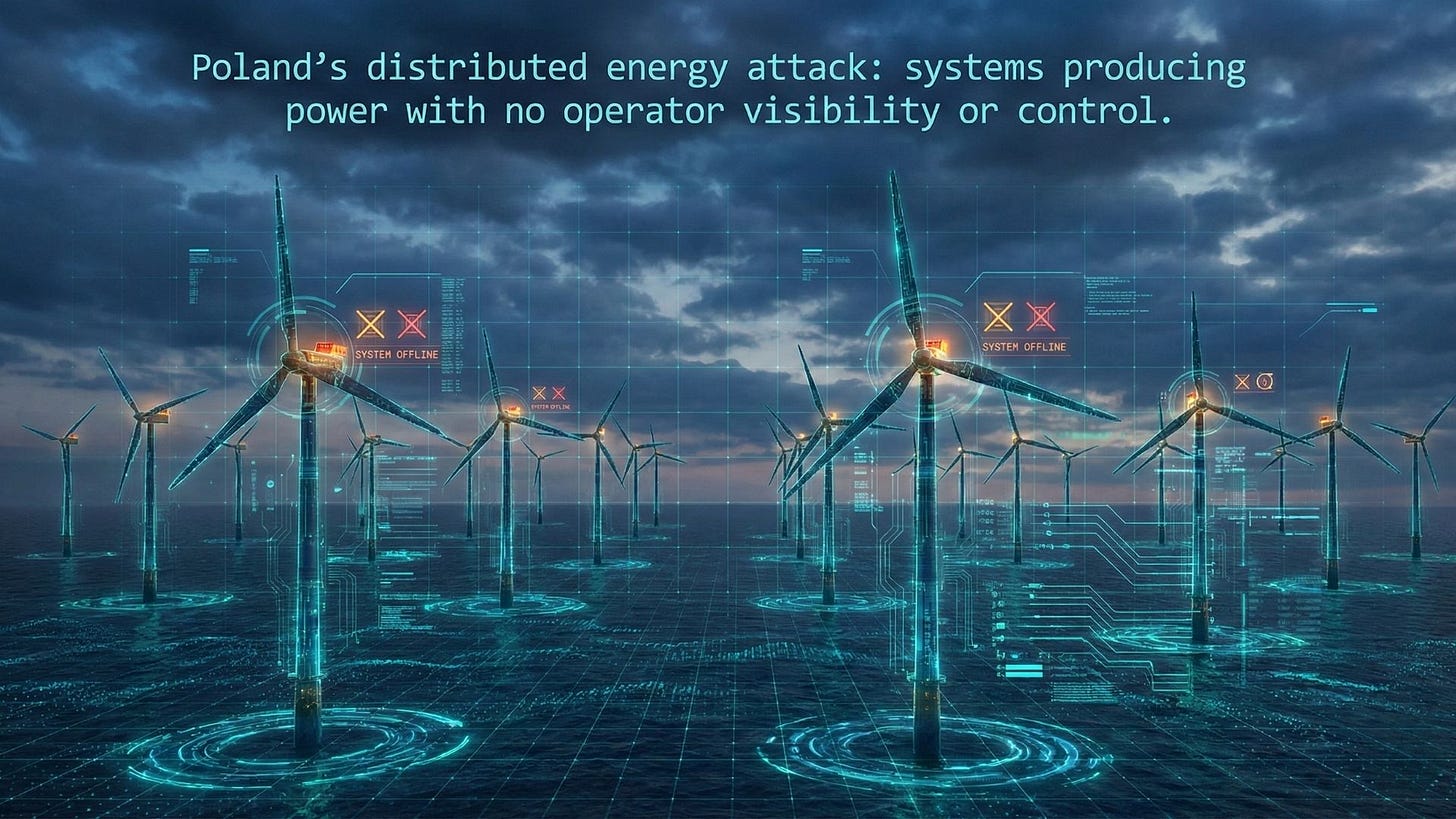
The payload was destructive, not espionage. Wiper malware corrupted firmware on remote terminal units (RTUs), deleted human-machine interface (HMI) data, and effectively blinded operators. The systems kept producing power — wind turbines still turned, solar panels still generated — but nobody could see what was happening or intervene if something went wrong [2].
The systems kept producing power. But nobody could see, monitor, or control them. That is a uniquely dangerous kind of failure.
The timing was not coincidental. Poland experienced extreme cold conditions in late December. Had the attack escalated to disrupt heating systems dependent on combined heat and power facilities, the humanitarian consequences could have been severe [1].
Why distributed energy is uniquely vulnerable
The shift to renewables has created what cybersecurity professionals call an “attack surface expansion problem.” Traditional power stations are few in number, physically secured, and staffed by specialists. Distributed energy resources are the opposite: numerous, geographically dispersed, remotely managed, and often operated by organisations without dedicated security teams.
This is the mid-market accessibility gap in action. A 50MW wind farm operator faces the same threat actors as National Grid, but with a fraction of the budget, expertise, and regulatory attention. Default credentials on OT devices from vendors including Hitachi, Mikronika, and Moxa were exploited in Poland — not because the technology was fundamentally flawed, but because smaller operators lacked the resources and processes to change them [2].
CISA’s emergency response alert, issued 9 February 2026, explicitly flagged DERs as a “novel target category” requiring urgent attention. The alert directed federal agencies and critical infrastructure operators to inventory internet-exposed edge devices, enforce MFA on network management interfaces, and mandate vendor enforcement of password changes during integration [1].
What this means for the UK
The UK’s net zero strategy depends heavily on distributed renewable infrastructure. Offshore and onshore wind, solar farms, battery storage, and smart grid systems are expanding rapidly. Each new facility extends the attack surface — and many are operated by mid-market companies without enterprise-grade cybersecurity programmes.
Three UK-specific risks demand attention.
First, the Cyber Security and Resilience Bill currently progressing through Parliament will, for the first time, bring managed service providers (MSPs) and data centres into scope for mandatory incident reporting. Initial notification within 24 hours of awareness, full report within 72 hours. Fines up to £17 million or 4% of worldwide turnover [5][6]. Energy operators relying on third-party MSPs for remote monitoring of DER facilities must ensure their contractual arrangements reflect these incoming obligations — before enforcement begins.
Second, the NCSC’s Cyber Assessment Framework (CAF) v4.0, updated August 2025, establishes requirements for a “definitive record” of OT assets — continuous, trustworthy, and segmented by consequence and exposure. The Poland attack succeeded precisely because asset visibility was inadequate. Operators did not know what devices were internet-exposed, what credentials they were running, or what firmware versions were installed [8].
Third, the convergence of IT and OT in renewable energy creates interdependencies that traditional segmentation models were not designed to handle. Building Information Modelling (BIM), digital twins, IoT sensors, and remote monitoring platforms create what researchers describe as “very high risk” network-of-systems architectures where a single compromise can cascade across entire project portfolios [17].
Analysis
In my view, the Poland attack represents a strategic inflection point rather than an isolated incident. Russian state actors have demonstrated they can — and will — target the distributed infrastructure that underpins modern energy systems. The tactical shift from centralised grid attacks to dispersed, under-resourced facilities is logical from an adversary’s perspective: lower defences, higher volume of targets, and a defender community that has not yet adapted.
The UK energy sector should treat this as a warning, not a headline. The organisations most at risk are not the large utilities with dedicated security operations centres. They are the mid-market operators, independent power producers, and community energy schemes that form the distributed backbone of our renewable infrastructure. These organisations need access to enterprise-grade security capabilities at mid-market price points — which is precisely where the current market fails them.
The regulatory environment is responding. The CSRB’s expanded scope, the NCSC’s updated CAF, and CISA’s emergency directives all point in the same direction: distributed energy security is no longer optional. But regulation alone does not secure systems. Implementation does.
Risks and constraints
Several important caveats apply. Attribution to Berserk Bear and Sandworm carries confirmed confidence from Polish government statements, but independent verification of specific TTPs remains ongoing. The full scope of the compromise may not yet be public — forensic analysis of 30 facilities takes considerable time.
The UK’s regulatory landscape is evolving. The CSRB’s secondary legislation (which will contain the detailed requirements for supply chain risk management) has not yet been published. Organisations should prepare for compliance but should not assume final requirements will mirror current drafts exactly.
Finally, the comparison between Polish and UK energy infrastructure has limits. Grid architectures, regulatory frameworks, and operational practices differ. Poland’s experience is instructive, not directly predictive. The principle — that distributed systems require distributed defence — is universal. The implementation details will be UK-specific.
What to do next
For boards and executives: Commission an immediate assessment of your organisation’s exposure to distributed OT infrastructure risk. Ask three questions: Do we know every internet-connected device in our operational technology estate? Do any of them run default credentials? What is our contractual position with MSPs regarding incident notification under the incoming CSRB? If you cannot answer all three with confidence, you have work to do.
For technical leaders: Inventory all internet-exposed edge devices (FortiGate, Cisco, SonicWall appliances) across your OT environment. Enforce MFA on every network management interface. Change every default credential — not next quarter, now. Implement firmware verification on OT devices and segment your network DMZ from internal environments. CISA’s emergency directive provides a practical checklist [1].
For mid-market energy operators: You face the same threat actors as national utilities with a fraction of their resources.
Prioritise three actions:
Asset visibility — you cannot defend what you cannot see;
Edge device hardening — unpatched, internet-exposed devices with default credentials are the primary attack vector;
MSP contract review — ensure your suppliers’ incident response obligations align with 24-hour CSRB notification requirements before enforcement begins.
Disclaimer: This article represents analysis based on publicly available information as of February 2026. It does not constitute legal, financial, or professional advice.
If your organisation needs support implementing OT security frameworks or preparing for CSRB compliance, Arkava helps mid-market enterprises turn cybersecurity investment into measurable resilience outcomes.
References
[1] CISA. “OT Vulnerabilities Alert — Poland Energy Grid Incident.” CISA, 9 February 2026.
[2] Industrial Cyber. “CISA Alerts on OT Vulnerabilities After Poland Energy Attack Damaged RTUs and Wiped HMI Data.” Industrial Cyber, 10 February 2026.
[5] Osborne Clarke. “UK Cyber Security and Resilience Bill: Pragmatic Overhaul or Regulatory Overload?” Osborne Clarke, 10 December 2025.
[6] OpenPolicy. “UK Cybersecurity Shake-Up: What a New Cyber Security & Resilience Bill Signals for 2026.” OpenPolicy, 19 November 2025.
[8] NCSC. “Annual Review 2025.” UK National Cyber Security Centre, October 2025.
[17] ScienceDirect. “A Perfect Storm: Digital Twins, Cybersecurity, and General Contracting Firms.” Developments in the Built Environment, 2024.