July '25 - Cyber Vulnerability round-up: Interlock, CRM Heists and the New Perimeter
Healthcare under siege, construction and government in the crosshairs, and a wave of supply-chain and CRM-driven breaches: this quarter’s data points to a step-change in how attackers infiltrate.
The signal: Interlock’s unusual playbook
Interlock, first observed in late September 2024, has rapidly evolved into one of 2025’s most consequential ransomware operations across North America and Europe. Investigators say its operators are financially motivated and opportunistic, leaning on a double-extortion model (steal and encrypt) while withholding any initial ransom amount. Instead, victims get a unique code and are pushed to a Tor (.onion) site to negotiate—an approach that complicates early incident response and public disclosure timelines.
What makes Interlock stand out is how it gets in. Beyond the usual phishing, it uses drive-by downloads from compromised but legitimate sites, often masquerading as browser or security updates. A now-notorious “ClickFix” ruse triggers a Base64-encoded PowerShell payload via a fake CAPTCHA, typically dropping a custom RAT before pivoting to lateral movement. Tooling observed being used post-compromise includes Cobalt Strike, AnyDesk and PuTTY for mobility; credential stealers and keyloggers for escalation; and AzCopy/Azure Storage Explorer for cloud exfiltration—before encryptors hit Windows and Linux VMs (file extensions such as “.interlock”/“.1nt3rlock”).
Why it matters: drive-by downloads and impersonated updates expand the attack surface beyond email, while cloud-native exfiltration (e.g., to Azure blobs) blurs traditional perimeter lines. This is incident response in the age of identity, browsers and SaaS.
Healthcare: still the soft underbelly
The healthcare sector remains uniquely exposed. A joint advisory from CISA, the FBI, HHS and MS-ISAC warns of Interlock’s “high-impact” activity against hospitals and health systems, where outages jeopardise care delivery and patient safety.
The headlines back it up. DaVita confirmed over one million people affected after an April attack; Interlock claimed the hit and began leaking files. Kettering Health disclosed an Interlock incident on 20 May, later reporting restoration milestones after weeks of disruption. Prior attacks include Texas Tech University Health Sciences Center, with ~1.46m records exposed. These are not isolated cases; they outline a pattern of data theft, operational disruption and prolonged recovery.
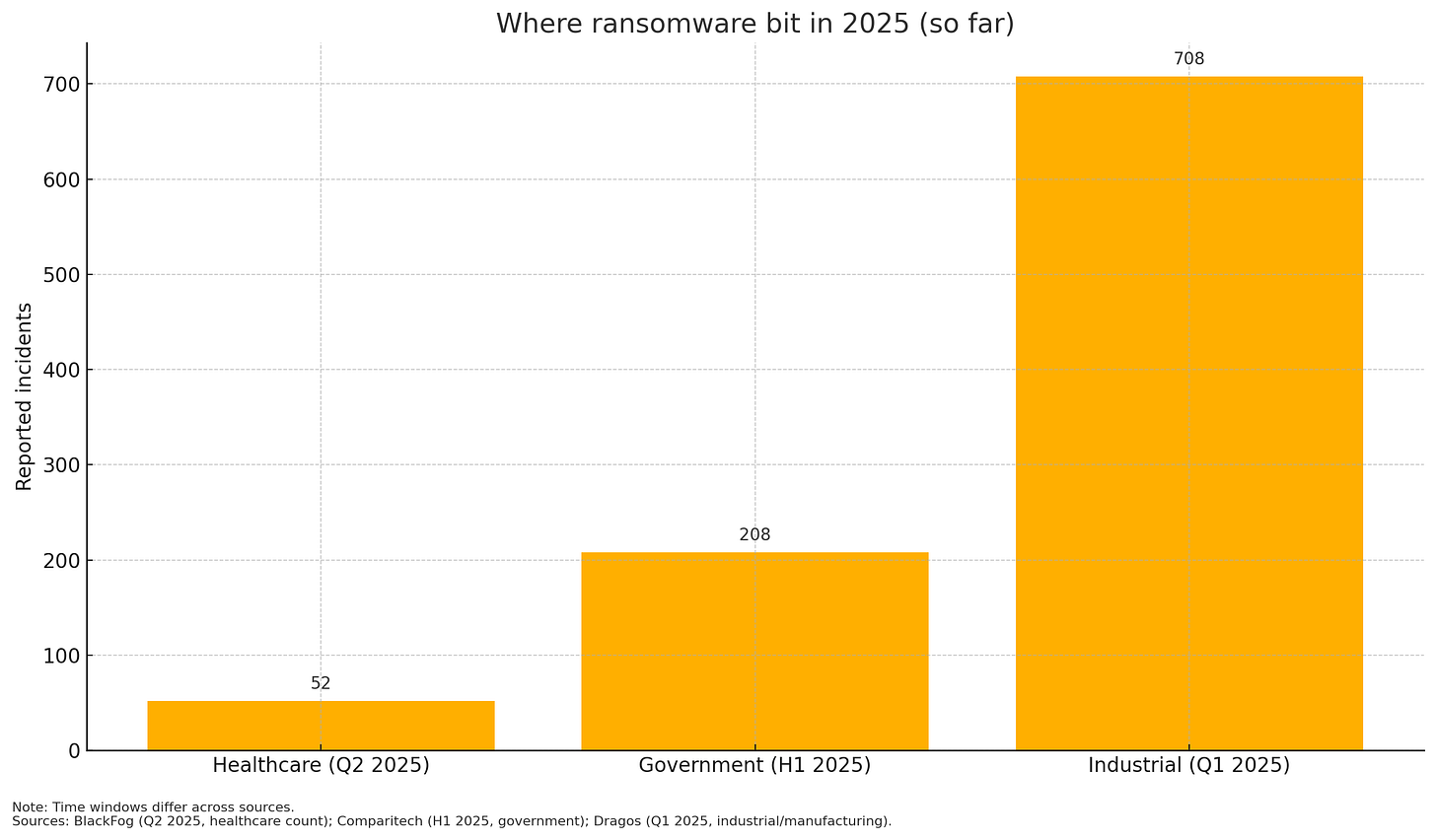
The sector-wide data is sobering. Publicly disclosed ransomware attacks jumped 63% in Q2 2025 versus Q2 2024, to 276 cases across sectors; healthcare led with 52 disclosed attacks, a new quarterly high in that dataset. Taken over H1, Comparitech’s rolling analysis shows a modest 4% YoY rise in healthcare ransomware incidents, a reminder that quarterly spikes can mask underlying volatility.
Operational take: hospitals must assume temporary loss of EHR and imaging systems, and plan paper-to-digital reconciliation, fail-open/closed protocols for critical care, and pre-approved mutual-aid arrangements.
Construction and government: two curves bending upward
Construction is now firmly on criminals’ shopping list. ReliaQuest’s industry survey0e found a 41% rise in construction organisations appearing on ransomware leak sites year-over-year, with credential exposure up 83% and now representing 75% of security alerts—a brutal indicator of how password reuse and infostealer logs feed extortion.
Government agencies are hardly spared: Comparitech tracks a 65% surge in ransomware attacks on government bodies in H1 2025 (208 incidents vs 126 a year earlier)—a telling mix of better disclosure and intensified targeting.
Why it matters: both sectors are rich in sensitive data and time-critical operations. Construction’s third-party sprawl (contractors, site systems, BIM and OT/IT overlap) and government’s public-interest obligations mean downtime translates quickly into economic, safety and political risk.
Industrial & manufacturing: the persistent hotspot
Ransomware continues to hammer industrial environments. Dragos identified 708 ransomware incidents impacting industrial entities in Q1 2025, up from ~600 in Q4 2024. Manufacturing absorbed 68% (480) of those cases—a reminder that OT-adjacent networks and production-critical IT remain frequent beachheads and bargaining chips.
No “new ICS-specific” encryptors were spotted that quarter, but the operational damage—from weather services outages to PCB production hits—shows how IT compromises ripple into OT, even when ICS is not the direct target.
Supply chain & the CRM heists: the new perimeter is other people’s systems
Two themes tie recent mega-breaches together: third-party platforms and CRM social engineering.
Allianz Life (US) disclosed on 16 July a vendor-side incident after adversaries impersonated IT helpdesk staff to extract credentials at a third-party cloud CRM provider, exposing data on most of its 1.4m US customers. Core Allianz systems were not breached.
Qantas (AU) said on 2 July that attackers breached a third-party call-centre platform, accessing a “significant” amount of personal data. Subsequent reporting tallied ~5.7 million customers affected. Payment and passport data were not in scope.
Louis Vuitton (LVMH) confirmed that regional breaches across the UK, South Korea, Turkey (and later Italy and Sweden) were tied to one incident—with attribution indicators pointing to ShinyHunters.
Google then admitted its corporate Salesforce instance was breached in the same ShinyHunters campaign it had been tracking—another case study in vishing + malicious connected apps targeting CRM. Google’s threat team has publicly detailed UNC6040’s voice-phishing playbook.
Bottom line: identity, browsers and SaaS admin consent flows are the true perimeter. Your risk is entangled with vendors’ admin practices, your users’ phone hygiene, and your CRM’s connected-app policies.
Threat actors and tactics: who’s doing what
Interlock: opportunistic double-extortion; rare drive-by entry; ClickFix social engineering; negotiation on Tor; VM-centric encryption across Windows and Linux. Healthcare is a frequent victim cohort.
ShinyHunters / UNC6040: CRM-focused vishing and OAuth/connected-app abuse; recent hits across luxury retail and tech—including Google and LVMH brands.
Scattered Spider: high-end social engineering and supply-chain compromise; cited around airline and insurance sector intrusions in late June/early July.
What to do next: a concise playbook
1) Kill the easy wins for attackers
Enforce phishing-resistant MFA on every externally reachable service and across SaaS admins/CRM.
Disable or strictly gate browser-delivered updates and PowerShell where not needed; monitor for Base64 PowerShell execution (Interlock hallmark).
2) Contain identity sprawl
Rotate and vault service accounts, especially those used by connected apps in Salesforce/CRM; require admin-consent workflows and app whitelists; continuously review OAuth grants.
3) Harden your data-exfil routes
Detect and rate-limit AzCopy/Azure Storage Explorer patterns, cloud egress to unfamiliar storage accounts, and anomalous bulk object operations.
4) Instrument where attacks actually land
Put EDR/XDR on VMs (Windows and Linux), not just workstations; monitor RDP/AnyDesk/PuTTY usage; baseline and alert on rare remote-admin tools.
5) Prepare for recovery, not just prevention
Maintain immutable, offline backups; test EHR/ERP failover and paper-to-digital workflows; rehearse crisis simulations through tabletops that include vendor-side breach scenarios and your regulatory notifications clock.
6) Fix construction/industrial blind spots
Segregate IT/OT, enforce least privilege on engineering workstations, and treat credential exposure as a standing incident (continuous dark-web credential harvesting and forced resets).
7) Vendor risk, but with teeth
Mandate phishing-resistant MFA, admin-consent controls and SIEM telemetry sharing in contracts; test providers’ incident comms and evidence preservation before you need them.
Quick sector snapshots (Q2–Q3 2025)
Healthcare: Interlock-driven surge; 52 disclosed ransomware attacks in Q2 (record in that dataset); ongoing patient-safety implications.
Construction: 41% YoY rise in leak-site victims; credentials are the fuel (83% increase; 75% of alerts).
Government: 65% YoY rise in H1 incidents; half publicly confirmed.
Industrial/Manufacturing: 708 incidents in Q1; manufacturing 68% (480).
Supply chain/CRM: Allianz Life (vendor CRM), Qantas (third-party call centre), Louis Vuitton (multi-country breach, single attack), Google (Salesforce) point to identity + SaaS + vendor as attack path of least resistance.
Editorial takeaway
Three forces define 2025’s threat landscape:
Interlock’s browser-and-cloud-savvy ransomware,
Credential-fuelled sector spikes (notably in construction and government),
The CRM/social-engineering wave that turns phone calls and OAuth prompts into data-leak factories. The message for boards and CISOs is simple: defend identities and SaaS with the same rigour once reserved for firewalls, and treat vendor controls as your own.
If you only do five things this month:
Enforce phishing-resistant MFA everywhere;
Lock down Customer Relationship Management tools connected-app consent;
Deploy Endpoint Detection and Response tools on VMs and watch for Base64 PowerShell;
Monitor cloud egress/AzCopy patterns;
Rehearse a vendor-side breach tabletop simulation exercise with legal and comms.